by Ryan Seguin
June 27, 2017
Rogue administrator accounts leave systems open to unauthorized access often without triggering network alarms. Systems Administrators can sometimes leave default administrator and guest accounts, which also compromises network access. Active scanning and log correlation assists analysts in identifying all of the administrator accounts in an environment. This report presents a summary of administrative account information, which can aid in identifying authorized and unauthorized access within the network.
In addition to reporting on unauthorized accounts, this report enables administrators to inventory the number of administrator accounts that have been purposefully or accidentally enabled across the network. Analysts can also find a list of vulnerabilities relating to administrative accounts to better understand the threats posed to their systems by admin accounts.
Information provided within this report contains details on administrative accounts that have been detected within the environment. Tenable Nessus actively scans and enumerates administrative accounts such as 'admin,' 'administrator' or 'root,' which are also default accounts that may need to be disabled as desired.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The report can be easily located in the Tenable.sc Feed under the category Monitoring.
The report requirements are:
- Tenable.sc 5.5
- Nessus 8.5.1
- LCE 6.0.0
Tenable.sc Continuous View (Tenable.sc CV) is the market-defining continuous network monitoring solution, and can assist in securing an organization’s internal network and effectively responding to intrusions and attacks. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Host data and data from other security products is analyzed to monitor the network for malware, intrusions and other forms of malicious activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to support proactive intrusion prevention efforts.
The following chapters are included in this report:
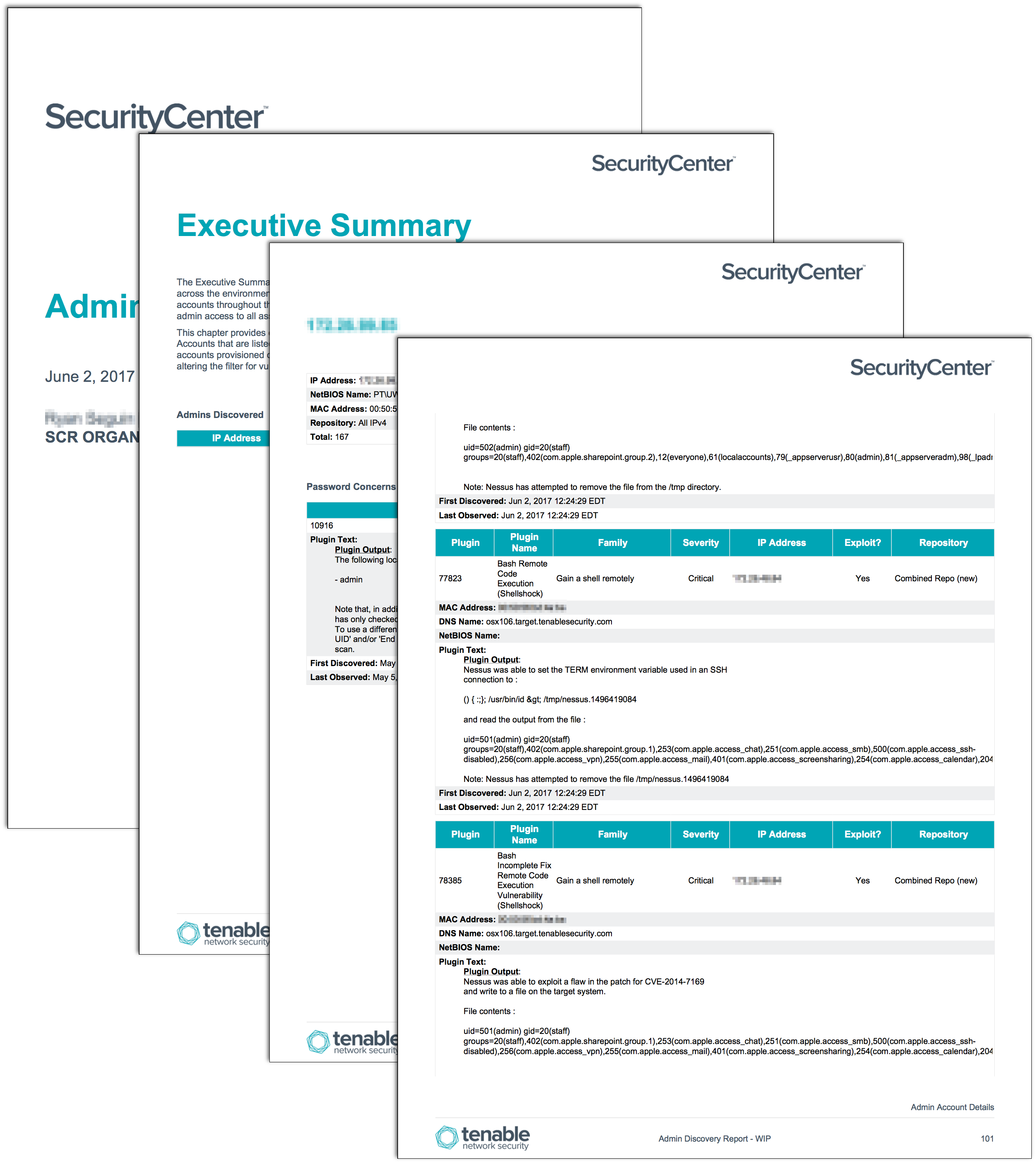
Executive Summary: The Executive Summary chapter provides detailed information about administrative accounts throughout the network. Information contained within this chapter presents a high-level overview of the admin access to all assets.
Admin Account Details: This chapter presents Administrative (including non-administrative) accounts that are enabled and whose passwords never expire, and any critical vulnerabilities (if any) that are associated with administrative accounts.
Members of Admin Groups: The following systems contain users that are also members of the Administrators Group.