by Stephanie Dunn
June 20, 2016
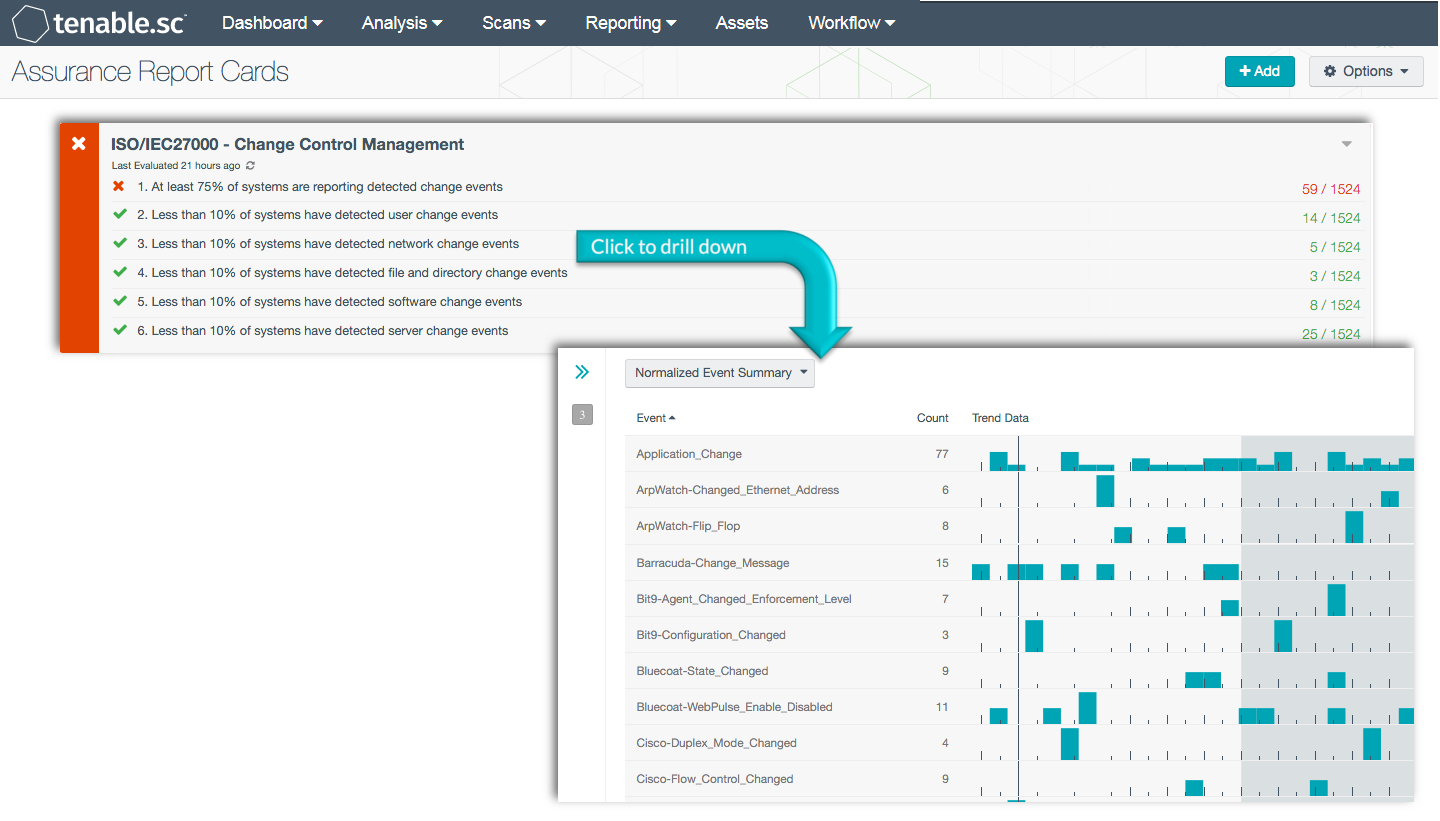
Managing change is a critical aspect that ensures organizations can accommodate new business requirements with little to no downtime. However, any unknown or unauthorized changes can severely impact the availability to critical devices and services. This Assurance Report Card (ARC) can alert organizations to a variety of configuration changes, which can help to determine whether current security policies in place are effective.
Change control management provides organizations with a comprehensive summary of changes across network devices, software, files, and user accounts. Any type of unintentional or unauthorized change can lead to weakened security controls and potentially devastating consequences for an organization. This ARC aligns with the change management controls of the ISO/IEC 27002 framework, which helps to ensure that configuration change control processes are in place, and configuration baselines are maintained.
Every change has a potential to disrupt critical services, and without controls in place incidents such as data leakage, project failures, misconfigured devices, and increased costs can occur. Implementing change management provides a structured approach to test whether the proposed changes will negatively impact end users. Using this approach, organizations will be able to identify issues and minimize risks associated with introducing new systems or services.
This ARC provides a baseline that can be used to measure the effectiveness of current change control policies in place. Each policy included within this ARC will help organizations identify specific change events across devices, user accounts, and security policies. User event changes will report on any password modifications, account name changes, and group memberships status changes that have occurred. Additional policy statements provide a report of any file and directory change events. Scanning for software changes will report on any applications that have been installed, along with any patches that may have been applied. Systems with detected change events will alert organizations to changes on devices forwarding logs to the Log Correlation Engine (LCE). Information provided within this ARC can assist organizations with improving change management and security configuration policies.
This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The ARC can be easily located in the Feed under the category Compliance. The ARC requirements are:
- Tenable.sc 5.3.2
- LCE 6.0.0
Tenable.sc Continuous View (Tenable.sc CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc CV is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Nessus Network Monitor (NNM) and Nessus both have the capability to discover operating systems, software, network devices, hypervisors, databases, tablets, phones, servers, and other critical assets. Tenable.sc CV allows for the most comprehensive and integrated view of changes across all network assets.
ARC Policy Statements:
At least 75% of systems are reporting detected change events: This policy statement displays the number of systems that have detected change events to the total systems. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Detected changes can alert analysts to possible data leakage, device changes, malicious activity, and more. Organizations should closely monitor all detected changes to determine whether the changes were authorized.
Less than 10% of systems have user change events: This policy statement displays the number of systems that have configuration change events to the total number of hosts detected on the network. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. User changes events trigger when a Windows security event log has determines that a user account was changed. Other user changes are the result of events such as user/group changes, password modifications, and account name changes. Unauthorized user changes can provide access to confidential data through escalated privileges. User and group permissions should be reviewed further to determine whether the changes were authorized.
Less than 10% of systems have network change events: This policy statement displays the number of systems that have network change events to the total number of hosts detected on the network. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. This policy statement utilizes the LCE “Network_Change” event, and triggers when host is up, changes to MAC addresses, and new hosts detected from network appliances.
Less than 10% of systems are reporting file and directory change events: This policy statement displays the number of systems that have file and directory change events to the total number of hosts detected on the network. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Any file or directory change should be closely monitored to detect possible privilege escalation, data leakage, or malicious activity. Organizations should review existing user access rights or clearance to prevent unauthorized access.
Less than 10% of systems are reporting software change events: This policy statement displays the number of systems that have software change events to the total number of hosts detected on the network. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Software change events can include software installations, application updates, and patches. Organizations should review software changes on a regular basis to detect the presence of any unauthorized or malicious software installed on the network.
Less than 10% of systems are reporting server change events: This policy statement displays the number of systems that have server change events to the total number of hosts detected on the network. If the policy statement requirement is met, the result is displayed in green; otherwise, the result is displayed in red. Server changes can include events such as registry changes, drive removal, hotfix installations, and server device changes. Changes on servers should be investigated immediately, as any unauthorized change may impact critical devices and services.