The Tenable Cyber Insurance Report provides measurements for the foundation of a cyber risk management program for organizations and is intended to be submitted on a voluntary basis to a cyber insurance provider as part of the underwriting process. Organizations are required to provide underwriters supporting evidence data that demonstrates the strength of their cybersecurity and risk management programs. Tenable.io provides organizations the ability to demonstrate risk management maturity with insurance companies. Insurance companies that issue cyber insurance policies have varying questionnaires and rating services that may not provide a complete picture of the organization’s cyber risk. The data provided in this report helps facilitate risk analysis based on vulnerabilities discovered using the Tenable vulnerability management platform, which provides information about the organization’s cyber risk exposure.
Organizations must know the existence and location of critical assets to ensure that assets are monitored and protected based on the business risk rating of each asset. Identifying assets facilitates vulnerability scanning and remediation by ensuring that scans are configured to probe for common weaknesses in the platform or application.
Risk Treatment is a strategy to appropriately manage threats to maximize profit and minimize financial loss. Cyber risk is associated with a level of severity of identified vulnerabilities that could potentially cause financial loss to the organization. Severity can be adjusted by accepting risk or adjusting vulnerability severity levels. This report has been configured to only report statistics on vulnerabilities and assets detected during the last 180 days. The report also takes a static approach by using the CVSSv3 Base Score to measure severity. The CVSS Base Score is divided into severity levels, 0 for Informational, 0.1-3.9 for Low, 4.0-6.9 for Medium, 7.0 to 9.9 for High, and 10 for Critical. These severity levels are used throughout this report.
The Cyber Insurance Report has read-only widgets that cannot be modified by Tenable.io users that provide underwriters insight into an organization's cyber risk posture. This report benefits both insurers and applicants seeking to demonstrate proactive risk reduction actions. Tenable.io users are not able to modify the report by adding additional filters using Tags or Custom Assets. This report displays all assets discovered using the sources Nessus, Nessus Agent, or Nessus Network Monitor (NNM).
Chapters
Discovery and Assessment – Organizations need to identify the existence and location of critical assets to ensure that said assets are monitored and protected based on the business risk rating of each asset. The widgets in this section provide details on the discovery and assessment of assets that demonstrate that the assets are monitored and protected based on the business risk rating of each asset.
Risk Prioritization – This section displays risk by Asset Criticality Rating, Common Vulnerability Scoring System (CVSS), exploitability by Attack Vector and Framework. Asset Criticality Rating (ACR) establishes the priority of each asset based on indicators of business value and criticality. ACR is based on several key metrics such as business purpose, asset type, location, connectivity, capabilities and third- party data.
Vulnerability Management – The information in this section describes risks associated with vulnerabilities that are included in exploit frameworks. Exploitability data for various exploit frameworks, including attack vectors, are leverage to communicate the current state of risk mitigation efforts.
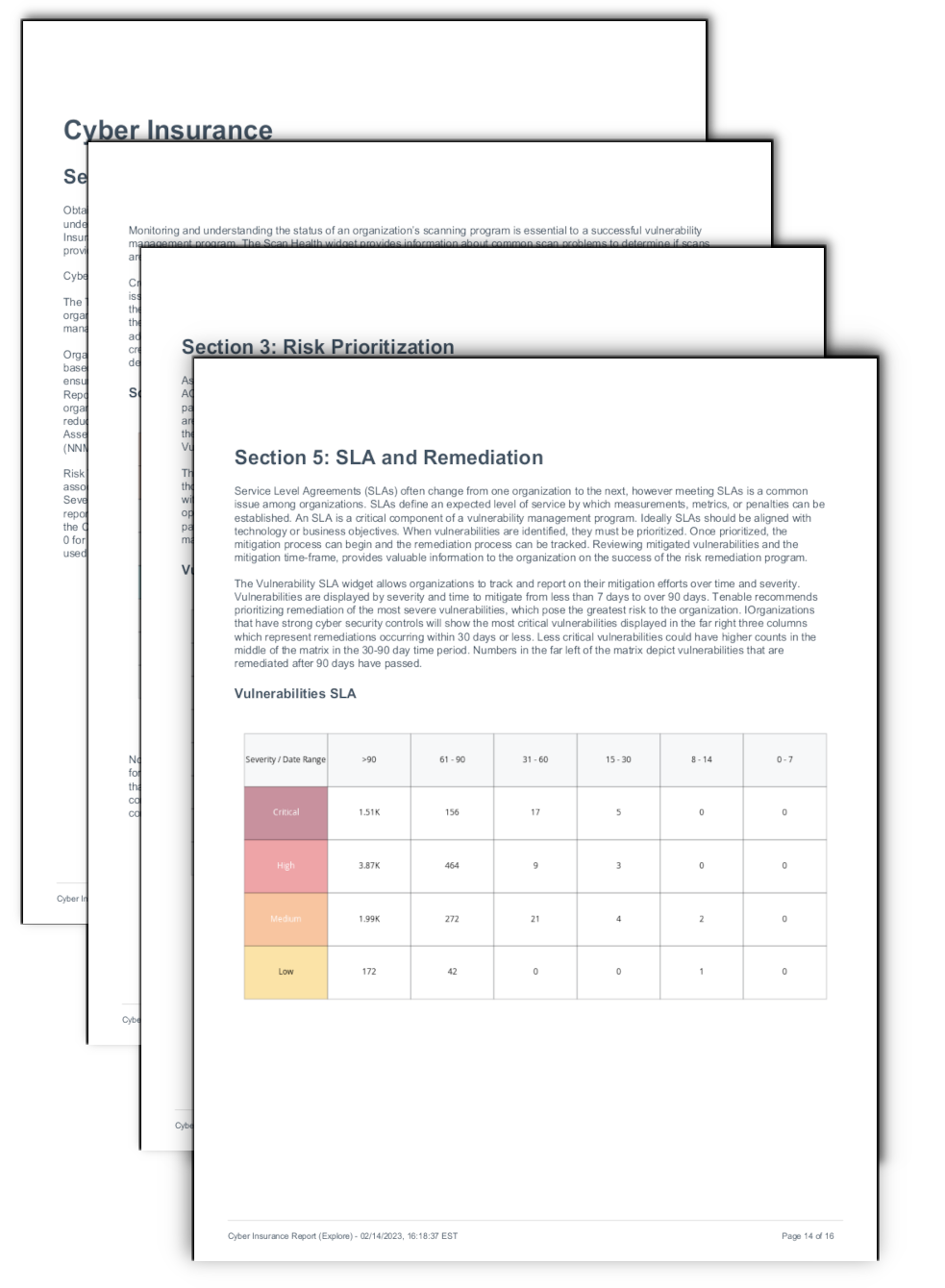
SLAs and Remediation – Service Level Agreements (SLAs) often change from one organization to the next, however meeting SLAs is a common issue among organizations. SLAs define an expected level of service by which measurements, metrics, or penalties can be established. An SLA is a critical component of a vulnerability management program. Reviewing mitigated vulnerabilities and the mitigation time-frame provides valuable information to the organization on the success of the risk remediation program, ensuring alignment with technology or business objectives.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success