Tenable
Security Center
Exponga y cierre sus debilidades cibernéticas con la solución de gestión de vulnerabilidades n.º 1 del mundo que se administra localmente
Reduzca el riesgo en su infraestructura de TI/OT. La solución que creó la categoría, continúa estableciendo los estándares para proteger a las empresas de la exposiciones cibernéticas críticas que aumentan el riesgo para el negocio.
La solución de gestión de vulnerabilidades n.º 1 del mundo que se administra localmente
La suite de Tenable Security Center
Personalizada para satisfacer sus necesidades, la suite de productos de Tenable Security Center le proporciona la visibilidad y el contexto que necesita para comprender su riesgo y reparar vulnerabilidades rápidamente.
Tenable Security Center
- Gestión de vulnerabilidades basada en el riesgo local.
- Visibilidad inmediata hacia su red con una cantidad ilimitada de Nessus Scanners.
- Información clara y procesable con tableros de control, informes y flujos de trabajo altamente personalizables.
- Identifique y priorice instantáneamente las vulnerabilidades mediante puntuaciones de riesgo incorporadas e inteligencia de amenazas contextualizada.
- Aceleración de la respuesta ante incidentes con alertas de configuración, notificaciones y emisión de tickets personalizables.
- Acceso gratuito a la API para integración de clientes, adquisición de datos y enriquecimiento de datos.
- Detección de activos desconocidos en su superficie de ataque externa.
Tenable Security Center Plus
Incluye todos los beneficios de Tenable Security Center, así como también los siguientes:
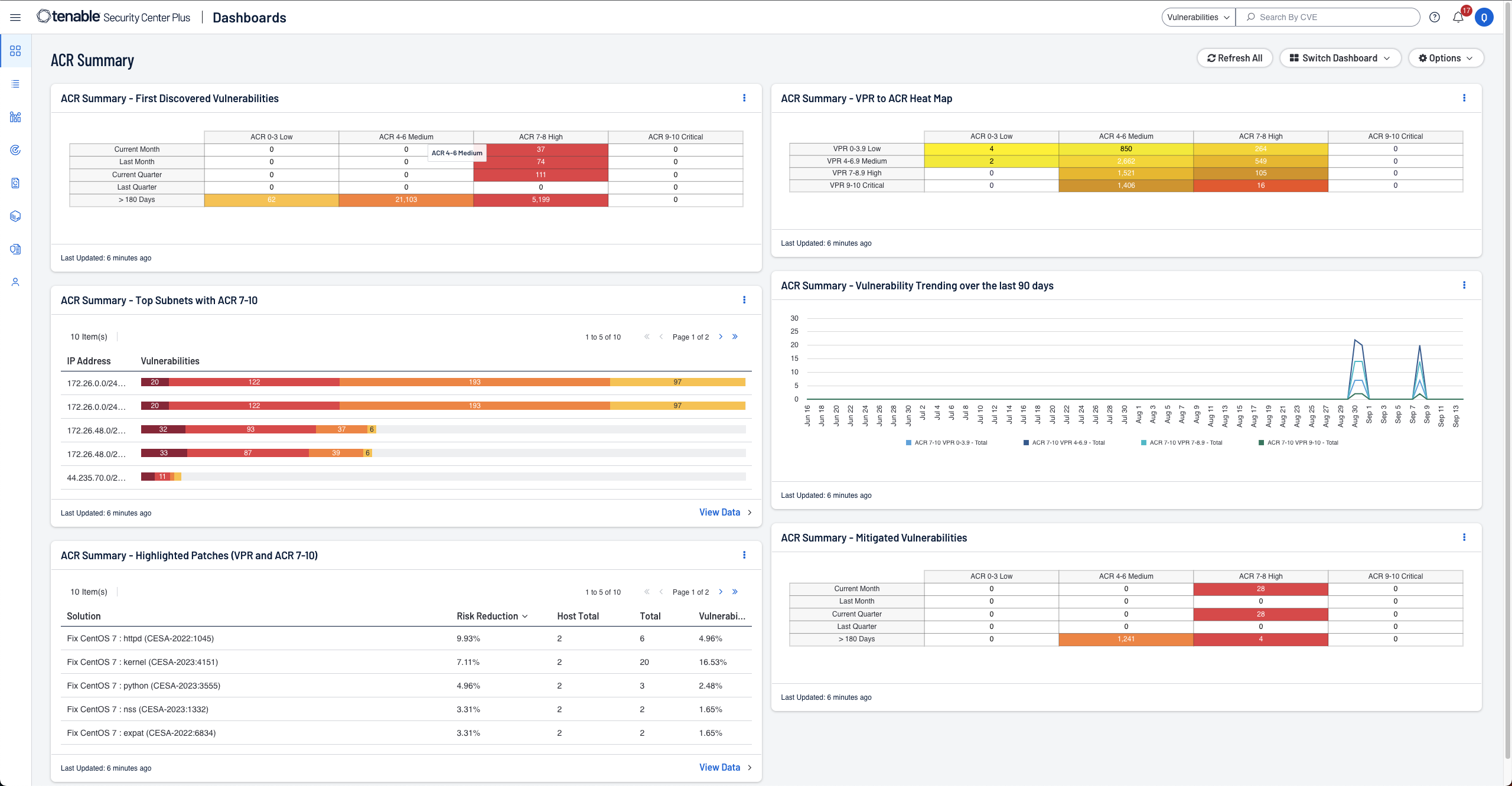
- Obtención de una comprensión y un contexto más profundos de sus activos mediante el Índice de Criticidad del Activo (ACR).
- Detección de activos y vulnerabilidades en tiempo real y monitoreo continuo para obtener el más alto nivel de visibilidad.
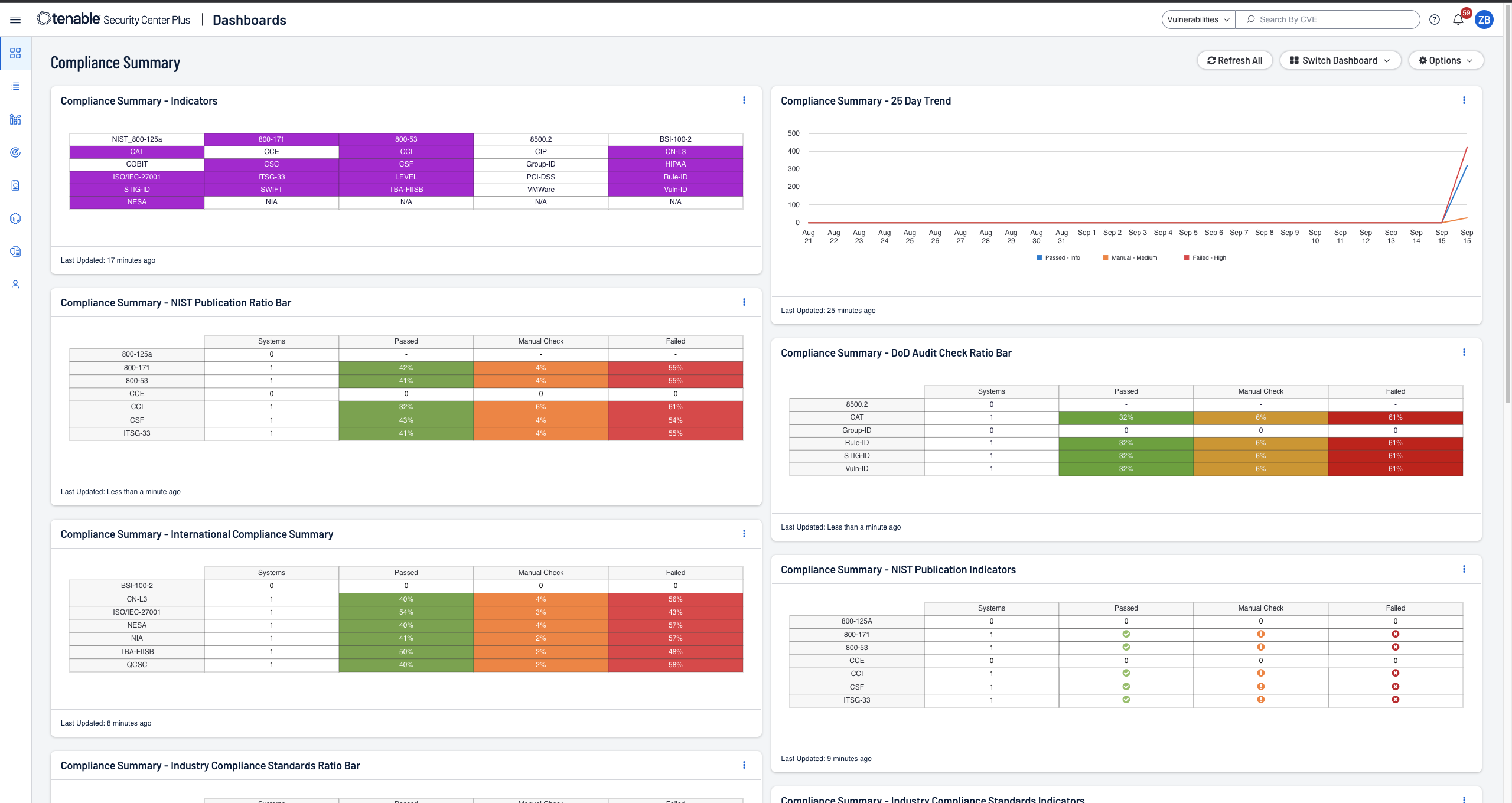
- Informes de cumplimiento optimizados con métricas en tiempo real y alertas proactivas sobre violaciones de seguridad.
- Detección en tiempo real de botnets y tráfico de comando y control.
- Identificación de recursos previamente desconocidos, cambios en el comportamiento y uso de nuevas aplicaciones.
Tenable Security Center Director
Para clientes con varias consolas de Tenable Security Center, Tenable Security Center Director está disponible como add-on de Tenable Security Center o Tenable Security Center Plus.
- Tablero de control único para ver y administrar su red en todas las consolas de Tenable Security Center.
- Vea fácilmente los escaneos para cada consola de Tenable Security Center desde una ubicación central.
- Información centralizada para facilitar la generación de informes y el tiempo de actividad de múltiples consolas, escáneres y activos
- Informes centralizados en varias consolas de Tenable Security Center para medir su riesgo cibernético con facilidad.
Mida y analice rápidamente los riesgos de seguridad y cumplimiento
Reseñas de Tenable Security Center
Tenable es el único proveedor que fue nombrado como Customers’ Choice en 2025 Gartner® Peer Insights™ Voice of the Customer dentro de la categoría de evaluación de vulnerabilidades

Tenable One
La única plataforma de gestión de exposición impulsada por IA del mundo
Tenable One reduce el riesgo cibernético al unificar la visibilidad, el análisis y la acción en materia de seguridad en toda la superficie de ataque, lo que ayuda a las organizaciones a detectar y corregir rápidamente las vulnerabilidades críticas.
Tenable Security Center se ha convertido en la voz de la verdad para nuestra red al brindar una capa adicional de información para hacernos responsables y validar el éxito de nuestro programa de seguridad ante nuestra junta directiva
Preguntas frecuentes
-
¿Qué es Tenable Security Center?
-
Tenable Security Center y Tenable Security Center Plus son las soluciones locales de gestión de vulnerabilidades de Tenable. Desarrollada con la tecnología de Nessus, líder en la industria, la familia de productos de Tenable Security Center identifica, investiga y prioriza las vulnerabilidades. De esta manera, le proporciona una visión basada en el riesgo de su postura de seguridad y cumplimiento. Para obtener más información sobre estas soluciones, consulte la hoja de datos de Tenable Security Center y la hoja de datos de Tenable Security Center Plus.
-
¿Cuál es la diferencia entre Tenable Security Center y Tenable Security Center Plus?
-
Tenable Security Center Plus es una plataforma de gestión de vulnerabilidades que se basa en la funcionalidad de Tenable Security Center y que incluye métricas de riesgo adicionales, como el Índice de Criticidad del Activo (Asset Criticality Rating, ACR), para ofrecer una capa adicional de contexto para sus activos y vulnerabilidades. Estas métricas proporcionan un abordaje más personalizado para su programa de gestión de vulnerabilidades, todo ello calculado en su instancia de Tenable Security Center Plus, por lo que sus datos permanecen en el ámbito local. Además, Tenable Security Center Plus puede integrarse con la plataforma de gestión de exposición de Tenable, Tenable One, con el fin de aumentar el valor de la información que proporciona Security Center Plus.
-
¿Tenable Security Center funciona con Tenable One?
-
¡Sí! Tenable Security Center Plus se integra con Tenable One para proporcionar implementaciones híbridas de gestión de vulnerabilidades y permitir que los clientes locales aprovechen una plataforma de gestión de exposición.
-
¿Qué es Tenable One?
-
Tenable One es una plataforma de gestión de exposición que ayuda a las organizaciones a obtener visibilidad a lo largo de la superficie de ataque moderna, enfocar los esfuerzos para prevenir ataques probables y comunicar con precisión el riesgo cibernético a fin de lograr un rendimiento óptimo del negocio. Esta plataforma proporciona la cobertura de vulnerabilidad más amplia, que abarca activos de TI, recursos en la nube, contenedores, aplicaciones web y sistemas de identidades. Se basa en la velocidad y la amplitud de la cobertura de vulnerabilidades de Tenable Research, y añade análisis completos para priorizar las acciones y comunicar el riesgo cibernético. Tenable One permite que las organizaciones hagan lo siguiente:
- Obtener visibilidad completa en toda la superficie de ataque moderna.
- Anticipar las amenazas y priorizar sus esfuerzos para evitar ataques.
- Comunicar el riesgo cibernético para tomar mejores decisiones.
-
¿Qué es Tenable Security Center Director?
-
Tenable Security Center Director es un complemento de Tenable Security Center. Este proporciona a los clientes comerciales una vista unificada de su red amplia y a menudo dispersa que comprende varias consolas de Tenable Security Center. Tenable Security Center Director ofrece visibilidad y gestión completas de sus instancias para que pueda concentrarse en la gestión de vulnerabilidades y reducir los gastos generales en tareas administrativas.
-
¿Tenable Security Center funciona junto con Tenable Web App Scanning?
-
Con Tenable Security Center, Tenable mejora sus defensas añadiendo seguridad de aplicaciones web local. Perfectamente integrado en la interfaz de usuario de Security Center, Tenable Web App Scanning lo empodera para identificar y abordar las vulnerabilidades en su red y aplicaciones web, reforzando su postura de seguridad mientras gestiona sus datos localmente.
Tenable Web App Scanning es una herramienta de pruebas de seguridad de aplicaciones dinámicas (DAST) que evalúa a profundidad las aplicaciones web. Rastrea la aplicación web para crear un mapa del sitio y luego escanea el front-end para detectar vulnerabilidades en el código personalizado y en los componentes de terceros.
-
¿Qué es la priorización predictiva y cómo ayuda a priorizar las vulnerabilidades?
-
La priorización predictiva combina datos de vulnerabilidades recolectados por Tenable con datos de vulnerabilidades y amenazas de terceros, y analiza todo esto con el algoritmo avanzado de ciencia de datos desarrollado por Tenable Research. Cada vulnerabilidad recibe un Índice de Priorización de Vulnerabilidades (VPR) que representa la probabilidad de que un atacante pueda explotar una vulnerabilidad dada en los próximos 28 días junto con su gravedad. Puede utilizar el VPR para comprender el riesgo cibernético real de las vulnerabilidades en sus entornos únicos, de modo que pueda priorizar los esfuerzos de corrección en las vulnerabilidades con el mayor impacto.
-
¿De qué manera Tenable Security Center encuentra activos y vulnerabilidades?
-
Gracias a una amplia gama de sensores, Tenable Security Center se encarga de la detección y la evaluación constantes de la red, los activos y las vulnerabilidades en tiempo real.
Tenable Security Center recopila datos de seguridad de toda su organización utilizando fuentes tales como las siguientes:
- Monitoreo pasivo: el monitoreo de los eventos y el tráfico de red en tiempo real proporciona información sobre qué activos están conectados a Internet y cómo se comunican. Identifica dispositivos o aplicaciones nuevos o nunca vistos, y detecta comportamientos sospechosos cuando suceden.
- Escaneo activo: analiza el estado de los activos minuciosamente a fin de identificar vulnerabilidades, errores de configuración, malware y otras debilidades.
- Datos de hosts: monitorea activamente los eventos y las actividades de los hosts, incluyendo información sobre el acceso y los cambios.
- Conectores inteligentes: al aprovechar sus otras inversiones en seguridad, Tenable Security Center puede integrar datos de seguridad adicionales con el fin de mejorar el contexto y el análisis. Ambos analizarán información de una amplia gama de fuentes de datos, incluyendo Active Directory (AD), bases de datos de gestión de configuración (CMDB), sistemas de gestión de parches, sistemas de gestión de dispositivos móviles (MDM), plataformas en la nube, aplicaciones web y más.
- Escaneo de agentes: audite instantáneamente los activos transitorios o difíciles de escanear que se conectan a Internet sin credenciales de forma intermitente. Una vez instalados, los agentes pueden ejecutar escaneos con credenciales sin tener que contar con credenciales de host continuas.
-
What are Tenable Agents? ¿Cómo funcionan con Tenable Security Center?
-
Tenable Agents are lightweight programs installed locally on a host — a laptop, virtual system, desktop and/or server. Los agentes reciben instrucciones de escaneo de un servidor central de Nessus Manager, realizan escaneos a nivel local e informan los resultados de vulnerabilidades, de cumplimiento y del sistema al servidor central. Tenable Agents are available with Tenable Vulnerability Management and Tenable Security Center.
Tenable Agents with Tenable Security Center increase scan coverage and remove blind spots by making it easier to scan problematic assets such as those needing ongoing host credentials and offline assets. Los agentes también permiten el escaneo simultáneo a gran escala con poco impacto en la red.
For more information on Tenable Agents, see the following resources:
-
¿Cuántos tipos diferentes de vulnerabilidades detecta Tenable Security Center?
-
Tenable Security Center está respaldado por Tenable Research, por lo que proporciona inteligencia de amenazas cibernéticas, información de ciencia de datos, alertas y boletines de seguridad de clase mundial. Tenable tiene uno de los conjuntos de datos de inteligencia y vulnerabilidades más extensos de la industria, con la cobertura CVE más alta de más de 79 000 CVE y más de 476 ataques de día cero dados a conocer desde enero de 2019. Tenable actualiza su base de datos de vulnerabilidades todos los días, a medida que surgen nuevas vulnerabilidades. Tenable Research realiza más de 100 detecciones nuevas cada semana.
-
¿Qué ocurre después de que Tenable Security Center detecta una vulnerabilidad?
-
Después de que Tenable Security Center detecta una vulnerabilidad, le proporciona información detallada para cada vulnerabilidad que se detecta, incluyendo lo siguiente:
- Información de la vulnerabilidad: Name and description of the vulnerability, remediation guidance, date of discovery and date of last vulnerability observation, CPE, date patch published, patching status, plugin ID and details.
- Información del host: Host name, affected hosts, IP address, DNS, Mac address, NetBIOS, repositor.
- Información sobre el riesgo: Vulnerability severity, VPR score, CVSS score and vectors, vulnerability age, known exploits, exploit code maturity, product coverage, threat intensity, threat recency, threat sources, percentage risk reduction associated with patching.
-
¿Cuáles son las capacidades de generación de informes de Tenable Security Center?
-
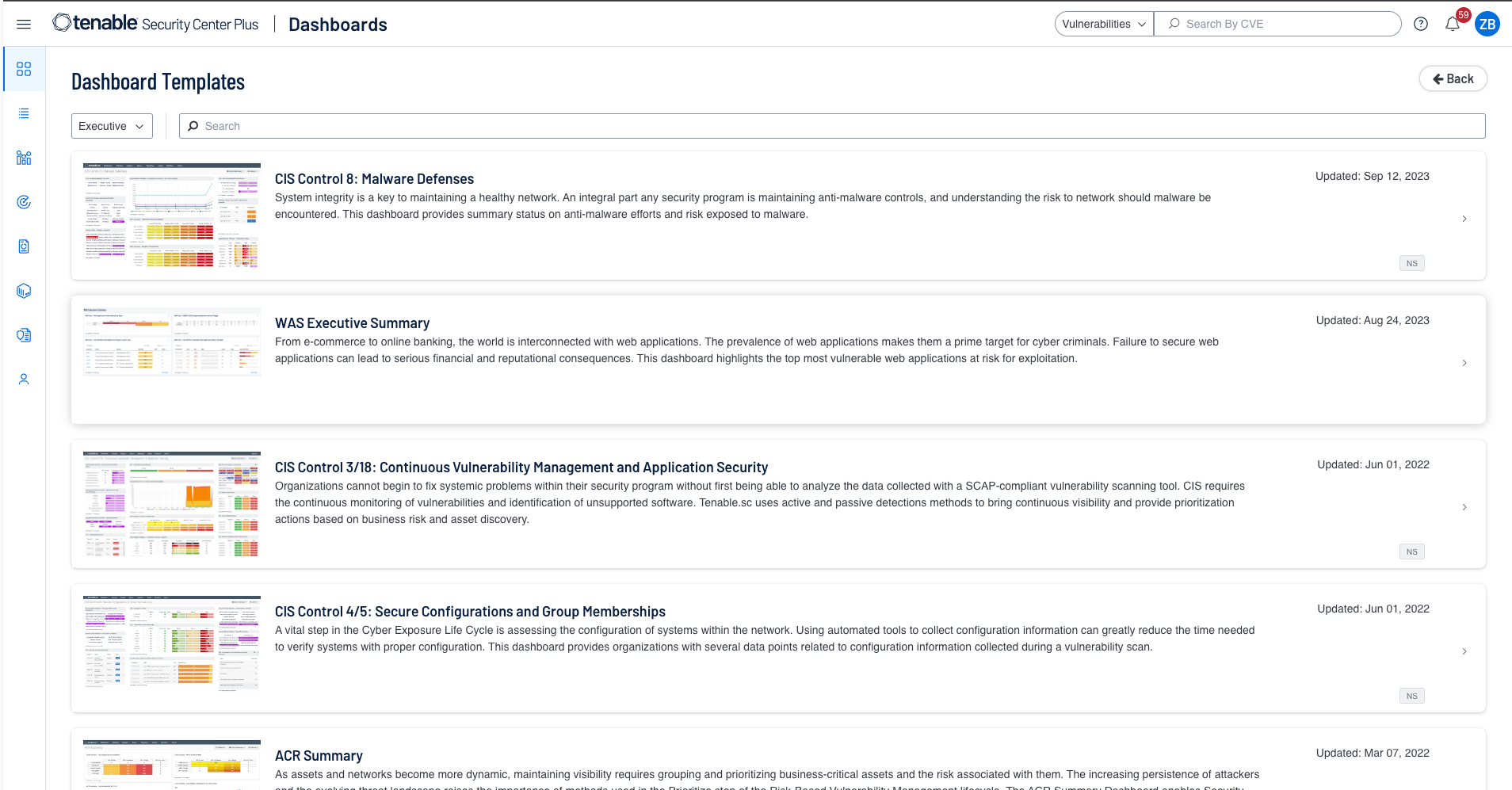
Tenable Security Center ofrece capacidades de generación de informes sumamente flexibles, ya que utiliza más de 350 plantillas diseñadas previamente y una interfaz de elaboración de informes fácil de usar para crear informes personalizados con facilidad. Los informes basados en HTML5 consolidan los datos de toda su organización para que pueda medir y analizar la eficacia de su seguridad. Cuando trabaja a partir de plantillas existentes, puede personalizar completamente los datos, eliminando o añadiendo ciertos componentes, o ajustando los filtros a fin de desarrollar informes que satisfagan sus diversas necesidades.
Puede desarrollar informes variados y personalizar cada uno de ellos para proporcionar una visión diferente de los datos recopilados, de modo que pueda ofrecer informes esclarecedores y oportunos a los equipos o a los tomadores de decisiones más adecuados dentro de su organización. Los informes tienen diferentes niveles de detalle, desde aquellos sumamente detallados hasta los resúmenes de alto nivel. Los informes están disponibles en los formatos estándar PDF y CSV. Usted puede programar y enviar informes por correo electrónico automáticamente, compartirlos con uno o más usuarios de consola especificados o publicarlos en uno o más sitios una vez finalicen.
También puede utilizar Tenable Security Center para generar informes de manera completa y automática acerca del cumplimiento de red con estándares complejos como PCI y NIST.
-
¿Puede Tenable Security Center ayudar a mantener el cumplimiento?
-
Sí. Tenable Security Center puede ayudar a mantener el cumplimiento. Le permite cumplir con la normativa con visibilidad inmediata hacia su postura de cumplimiento. Puede demostrar el cumplimiento de manera sencilla con verificaciones predefinidas con respecto a los estándares de la industria y los requisitos normativos como ISO/IEC 27001/27002, PCI, NIST Cybersecurity Framework, NIST SP 800-171 y controles de seguridad crítica de CIS.
Tenable Security Center proporciona informes y tableros de control totalmente personalizables y listos para usar, que son específicos de los principales estándares de seguridad y requisitos de cumplimiento. Puede utilizarlos “tal cual” o adaptarlos fácilmente para satisfacer sus necesidades específicas de seguridad y de negocios. Por ejemplo, puede crear fácilmente informes y tableros de control específicos para líneas de negocios individuales.
-
¿Qué es Tenable AI Aware?
-
Tenable AI Aware es una funcionalidad dentro de Tenable Vulnerability Management y Tenable Security Center que ayuda a las organizaciones a monitorear y mitigar los riesgos asociados con la rápida adopción de tecnologías de IA. Aprovecha tecnologías de detección avanzada que incluyen agentes, monitoreo pasivo de red, pruebas de seguridad de aplicaciones dinámicas y motores de escaneo distribuidos para sacar a la luz soluciones de IA no autorizadas, identificar vulnerabilidades de IA y detectar desarrollos imprevistos de IA o modelos extensos de lenguaje (LLM). AI Aware proporciona un abordaje completo de seguridad primero para gestionar los riesgos relacionados con la IA al ofrecer una visibilidad profunda del software, las bibliotecas y los plug-ins de navegador de IA en el ecosistema digital de una organización. Puede encontrar más información de Tenable AI Aware aquí.
-
¿Qué es la gestión de superficie de ataque externa (EASM)?
-
External Attack Surface Management s a capability offered by Tenable that provides visibility into blind spots outside of your network perimeter. Esto permite a los clientes analizar su dominio para encontrar activos conectados a Internet desconocidos que pueden suponer un alto riesgo para su organización.
-
¿Está incluida la gestión de superficie de ataque externa en Tenable Security Center?
-
Sí. Tenable Security Center ofrece capacidades de gestión de superficie de ataque externa. En el caso de que requiera dominios adicionales, frecuencia y/o metadatos en sus resultados, puede adquirir nuestros complementos de Tenable Attack Surface Management.
-
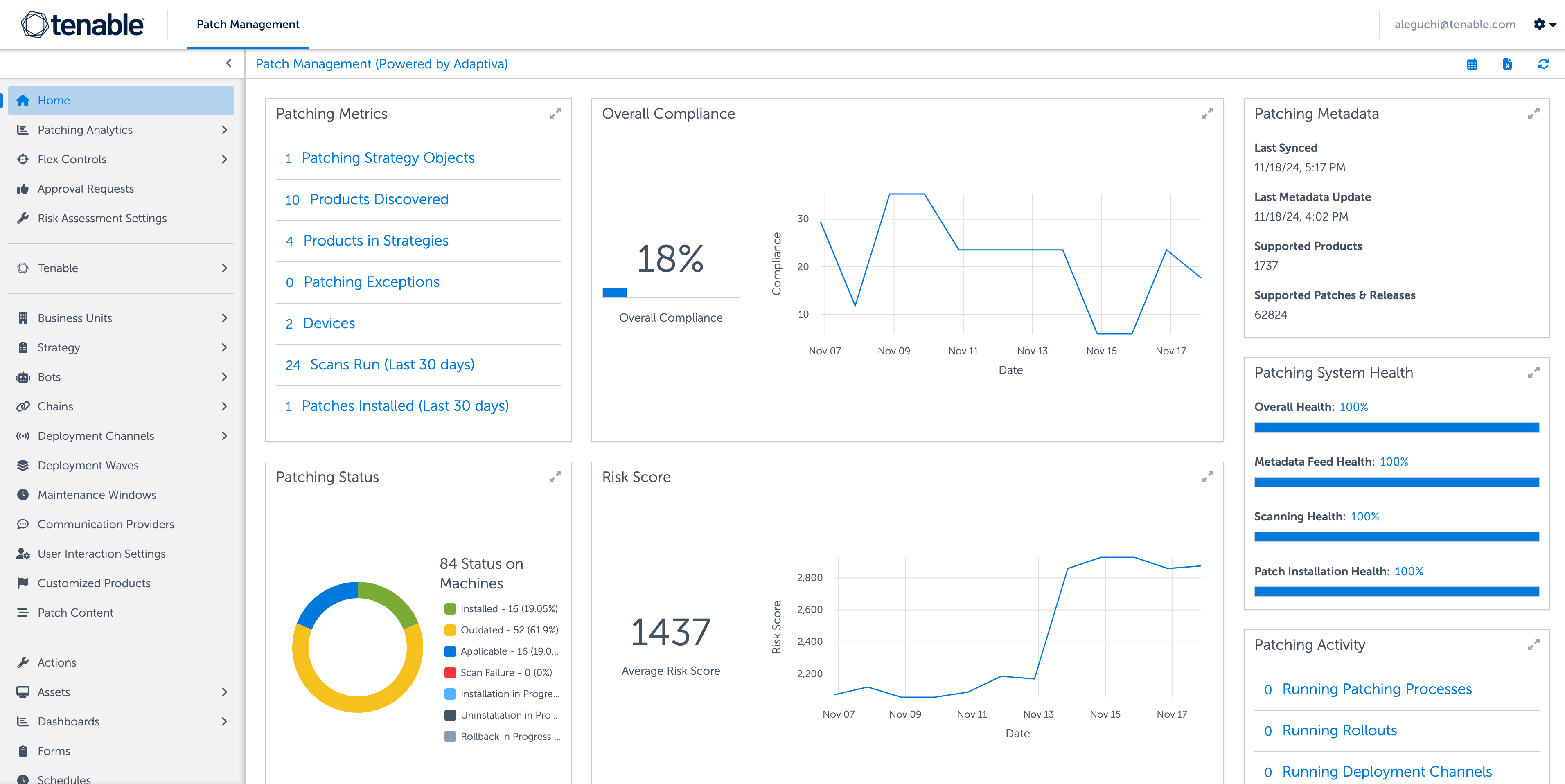
¿Qué es Tenable Patch Management?
-
Tenable Patch Management es un módulo de gestión de parches que reúne las capacidades de priorización líderes en la industria de Tenable con la funcionalidad de colocación de parches autónoma. La correlación automatizada entre vulnerabilidades y la acción de corrección más actualizada ayudan a sus equipos a superar el cuello de botella que puede presentarse entre la priorización y la corrección de vulnerabilidades. Diseñado para escalar hacia arriba o hacia abajo para adaptarse a cualquier organización, Tenable Patch Management permite a su organización gestionar con precisión la configuración con granularidad en torno a implementaciones, pruebas, aprobaciones, aplicaciones y más.
Para aprovechar Tenable Patch Management, necesita una licencia de Tenable Security Center, Tenable Vulnerability Management, Tenable One o Tenable Enclave Security. Más información aquí.
-
¿Tenable Security Center se integra con otros productos?
-
Sí. Tenable Security Center se integra con otros productos. La suite proporciona integraciones listas para usar para aprovechar los conocimientos de vulnerabilidades de Tenable con emisión de tickets, gestión de parches, SIEM, SOAR y otros productos de terceros. Visite la página Ecosistema tecnológico para obtener más información sobre las integraciones disponibles y los socios del ecosistema. También puede utilizar la API de Tenable Security Center para desarrollar integraciones personalizadas.
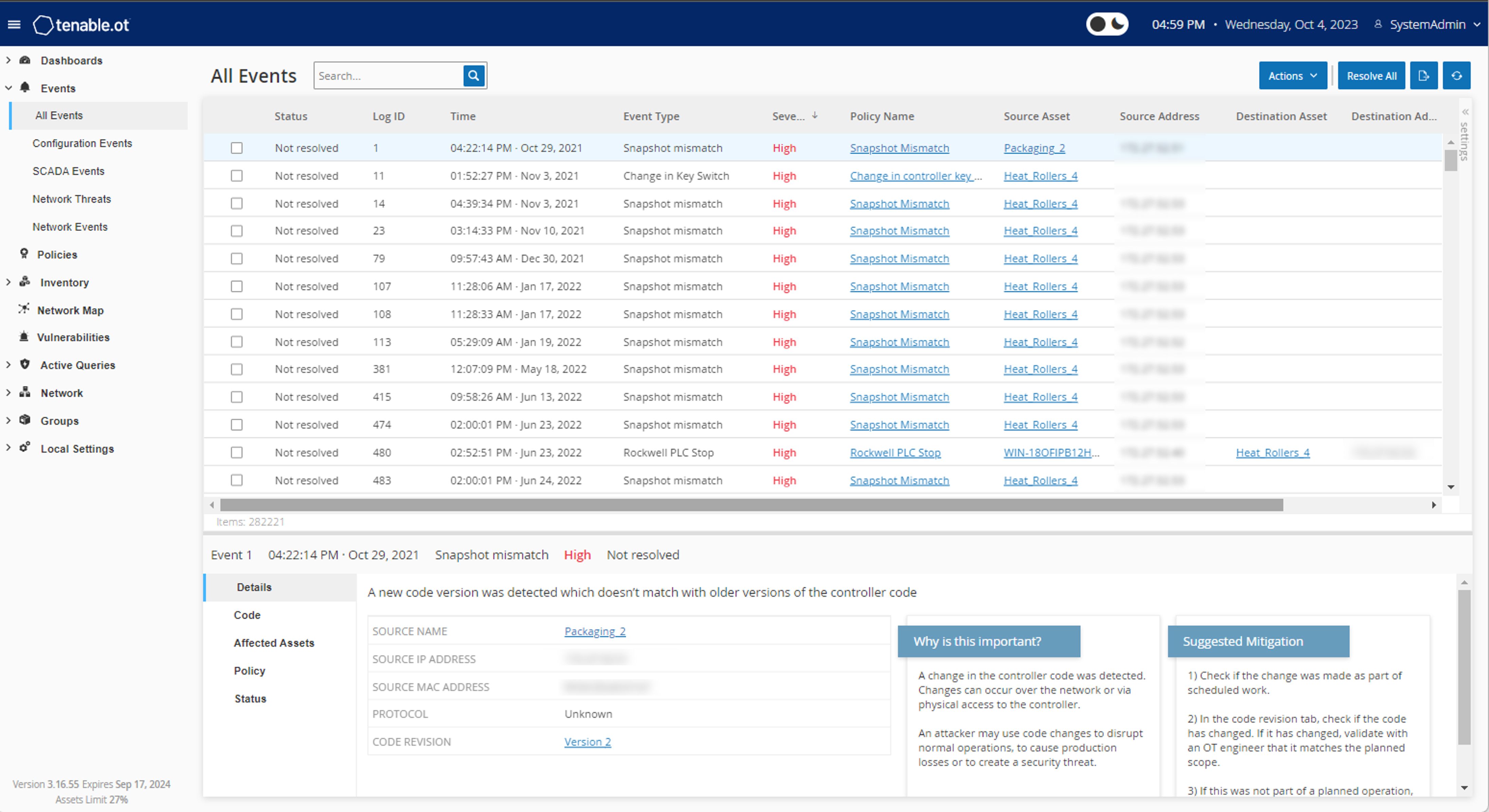
Además, Tenable Security Center cuenta con integraciones incorporadas con Tenable OT Security, Tenable Web App Scanning y Tenable Patch Management. Tenable Security Center Plus se integra con Tenable One, que proporciona implementaciones híbridas de gestión de vulnerabilidades y permite a los clientes locales aprovechar una plataforma de gestión de exposición.
-
¿Cuál es el precio y la licencia de Tenable Security Center?
- Tenable Security Center ofrece licencia por suscripción anual y precio por IP. También hay licencias perpetuas disponibles.
-
¿Dónde puedo encontrar documentación sobre Tenable Security Center?
-
Puede encontrar la documentación técnica de Tenable Security Center y todos los productos de Tenable en https://docs.tenable.com/.
-
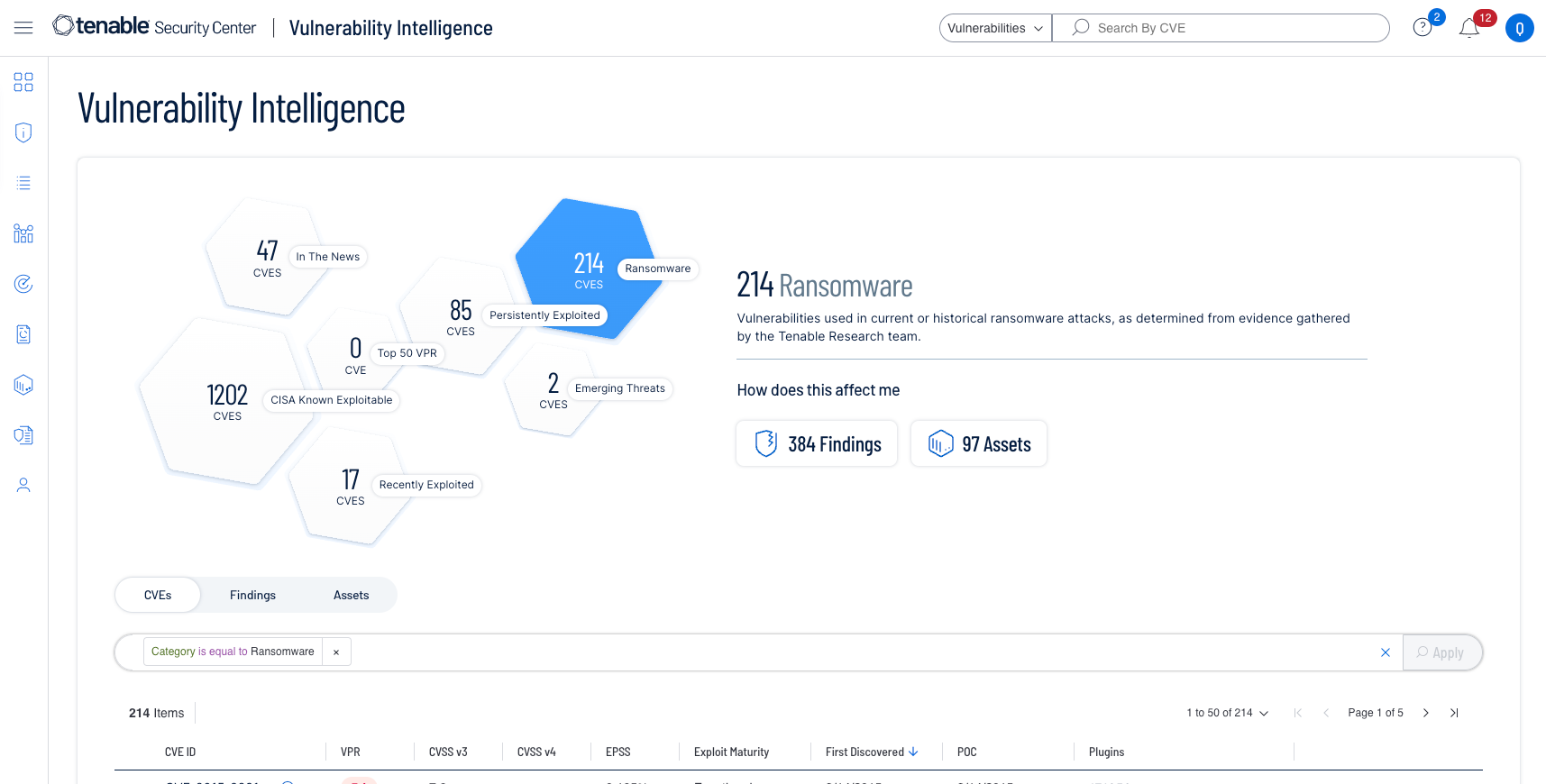
¿Qué es Vulnerability Intelligence (Inteligencia de vulnerabilidades?
-
Vulnerability Intelligence (Inteligencia de vulnerabilidades) adquiere información procesable para la gestión de vulnerabilidades con base tanto en fuentes de datos externas como en datos de vulnerabilidades internos. Proporciona un contexto vital sobre cualquier vulnerabilidad dada para comprender la probabilidad de que un atacante la explote y una visualización del impacto en su entorno.
Vulnerability Intelligence (Inteligencia de vulnerabilidades) reúne la amplia información de investigación de vulnerabilidades, el conocimiento de ciencia de datos, la respuesta de seguridad y los datos de gestión de vulnerabilidades de Tenable en un solo lugar unificado. Puede buscar, contextualizar y responder fácilmente a las vulnerabilidades con base en esta rica inteligencia e informar a la gerencia el impacto que tienen las vulnerabilidades en su organización.
Obtenga más información acerca de Vulnerability Intelligence







Tenable One
Solicitar demostración
La plataforma de gestión de exposición impulsada por IA líder en el mundo.
Gracias
Gracias por su interés en Tenable One.
Un representante se pondrá en contacto con usted en breve.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success