Discover, prioritize, and remediate vulnerabilities, misconfigurations, identity,
and
data risks, across
multi-cloud environments.
-
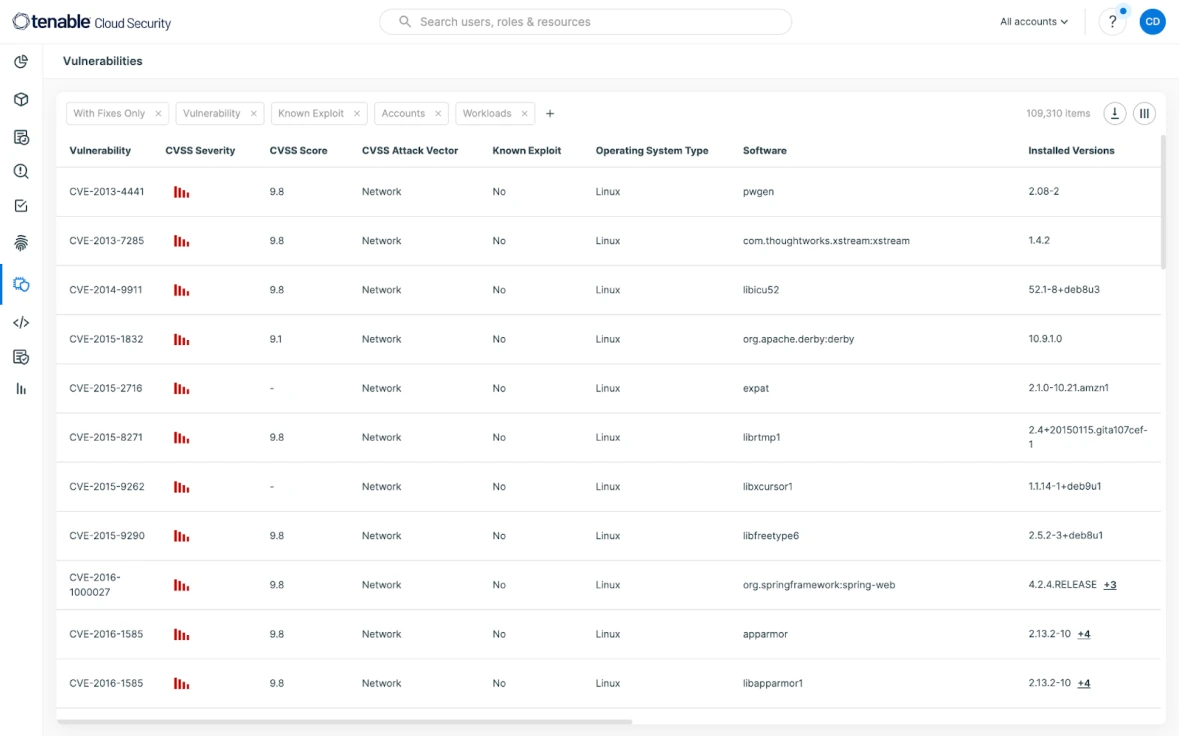
Cloud-Native Vulnerability Mgmt. Get prioritized visibility into every cloud resource
from development to runtime. -
Enforce Least Privilege. Leverage the intuitive UI to attain the least privilege without disrupting productivity.
-
Automate Compliance. Eliminate audit fire drills. Verify and automatically
report on compliance frameworks.
Solicite una demostración de Tenable Cloud Security
¡Una excepcional seguridad unificada en la nube le espera!
We'll show you exactly how Tenable Cloud Security helps you deliver
multi-cloud asset discovery, prioritized risk assessments and
automated compliance/audit
reports.
Join 40,000+ organizations automating their cloud security with the leading independent provider

Seguridad en la nube que se adapta a su situación particular
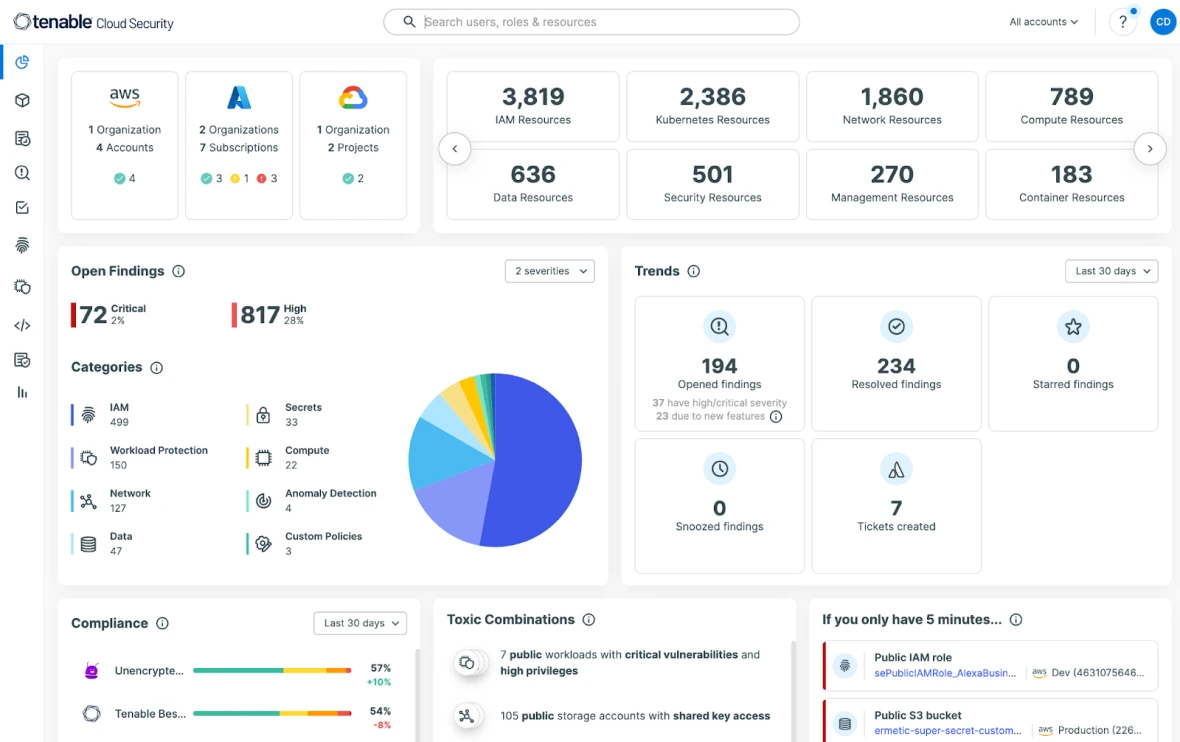
Get full visibility across AWS, Azure, GCP, and Oracle Cloud Infrastructure (OCI) with 100% agentless scanning. Continuously discover your cloud environment across infrastructure, workloads, identities, and data, powerfully visualizing all your cloud assets. Obtain a unified view that simplifies your team’s understanding of even the most complex issues.
Try for free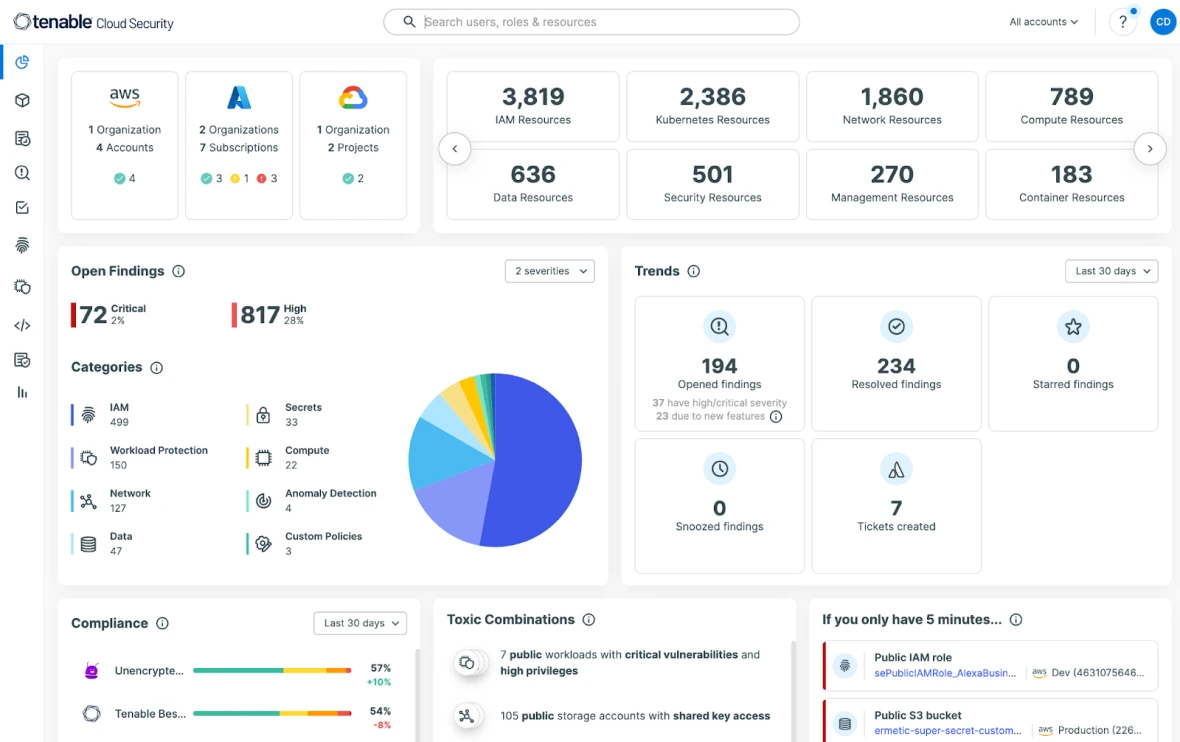
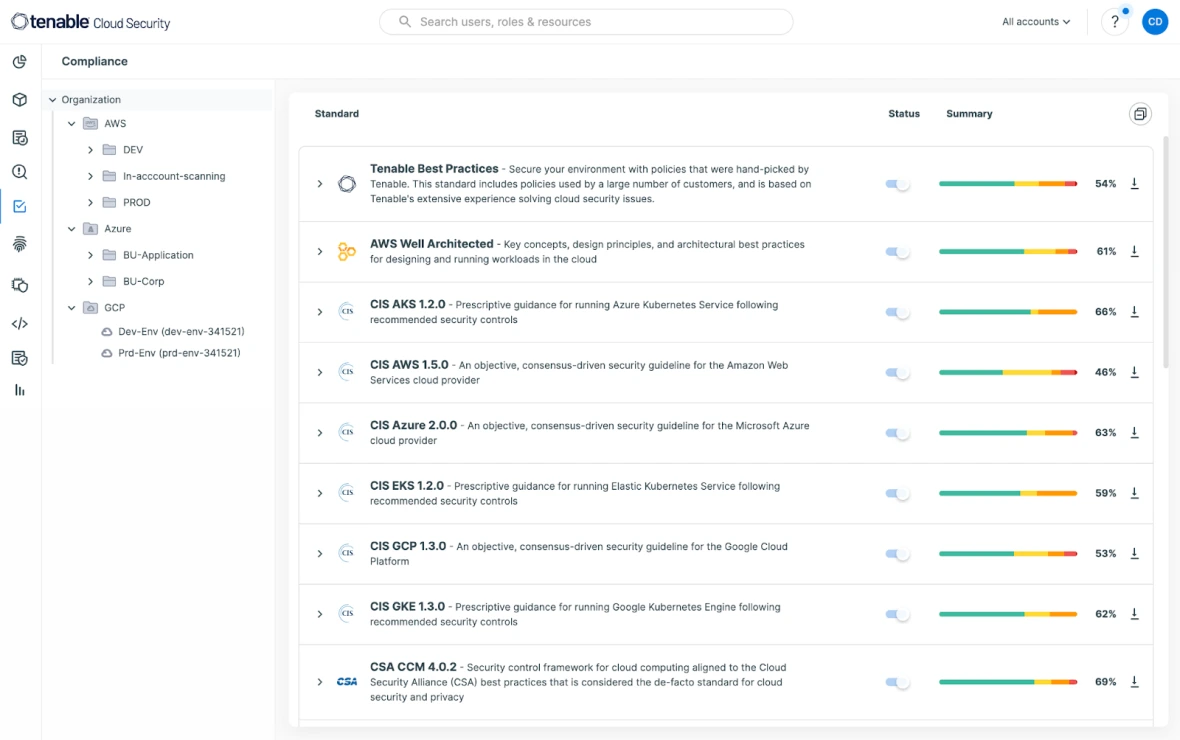
Monitoree el riesgo revisando y evaluando continuamente los ajustes y la configuración del entorno en la nube. Al mapear los riesgos detectados contra los estándares y políticas de seguridad, puede lograr y mantener el cumplimiento y abordar fácilmente las auditorías en entornos multinube. Saque provecho de la generación de informes desarrollada previamente para más de 20 marcos de cumplimiento, incluidos SOC-2, RGPD, PCI DSS, HIPAA, NYDFS y otros.
Try for free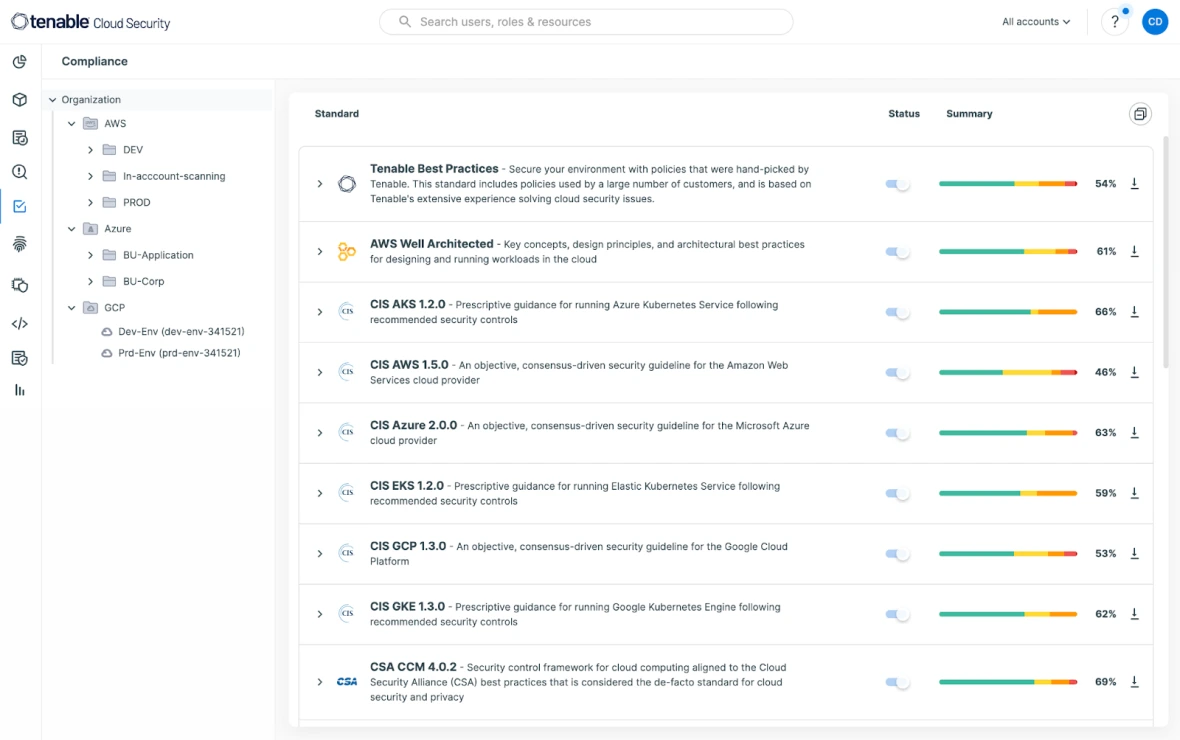
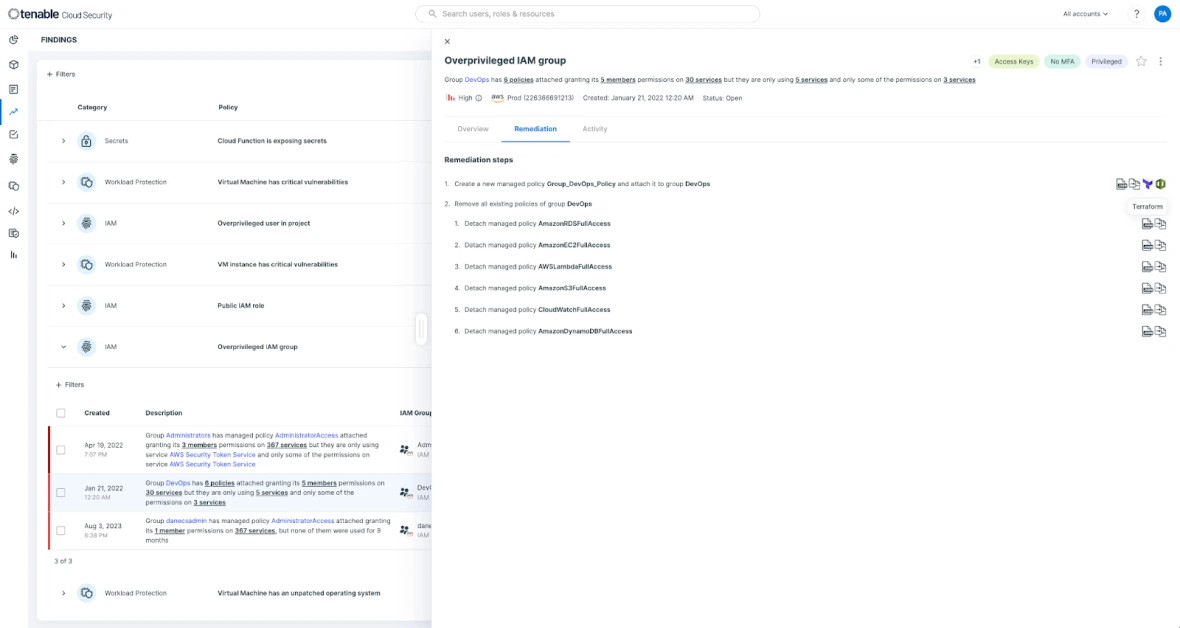
Tenable is a cloud security solution that allows you to focus on the risks that matter most. Tenable Cloud Security gives users deeply prioritized findings that empower Security and DevSecOps teams to automate threat detection and remediation efforts at scale. Mitigate and remediate risky privileges and faulty configurations using auto-generated and customizable policies by seamlessly integrating across ticketing, CI/CD pipelines, IaC, and other workflows.
Try for free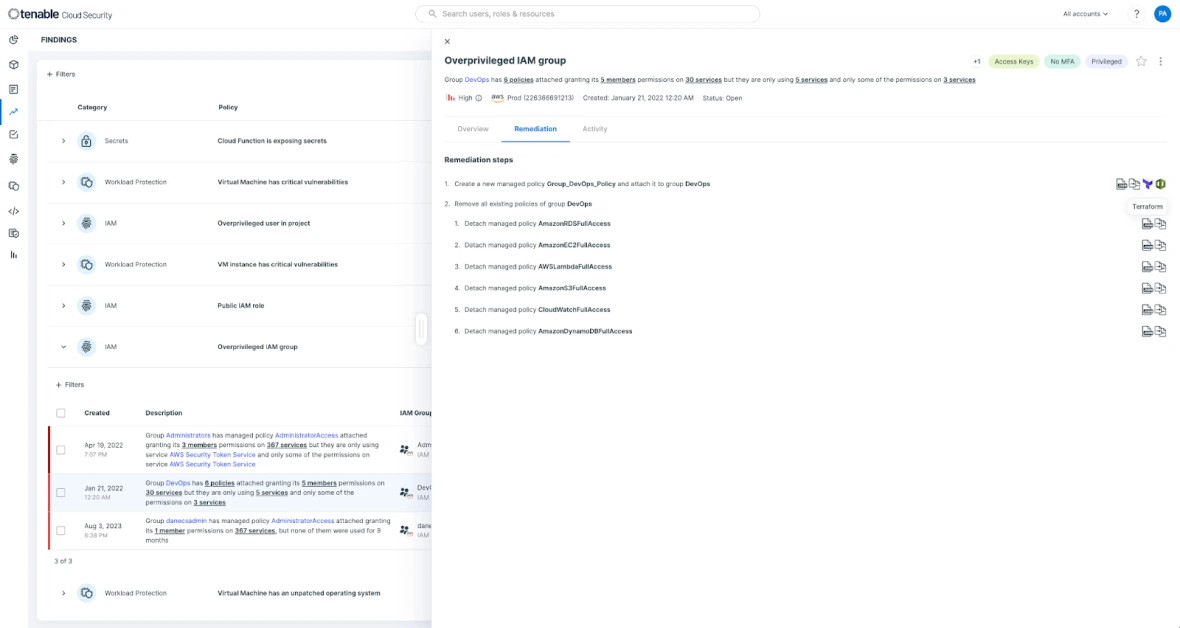
Reconozca las actividades anómalas y sospechosas evaluando continuamente el riesgo frente a las bases de referencia del comportamiento. Analyze cloud provider logs and link cloud threats with underlying architecture to show the context associated with each risk quickly.
Try for free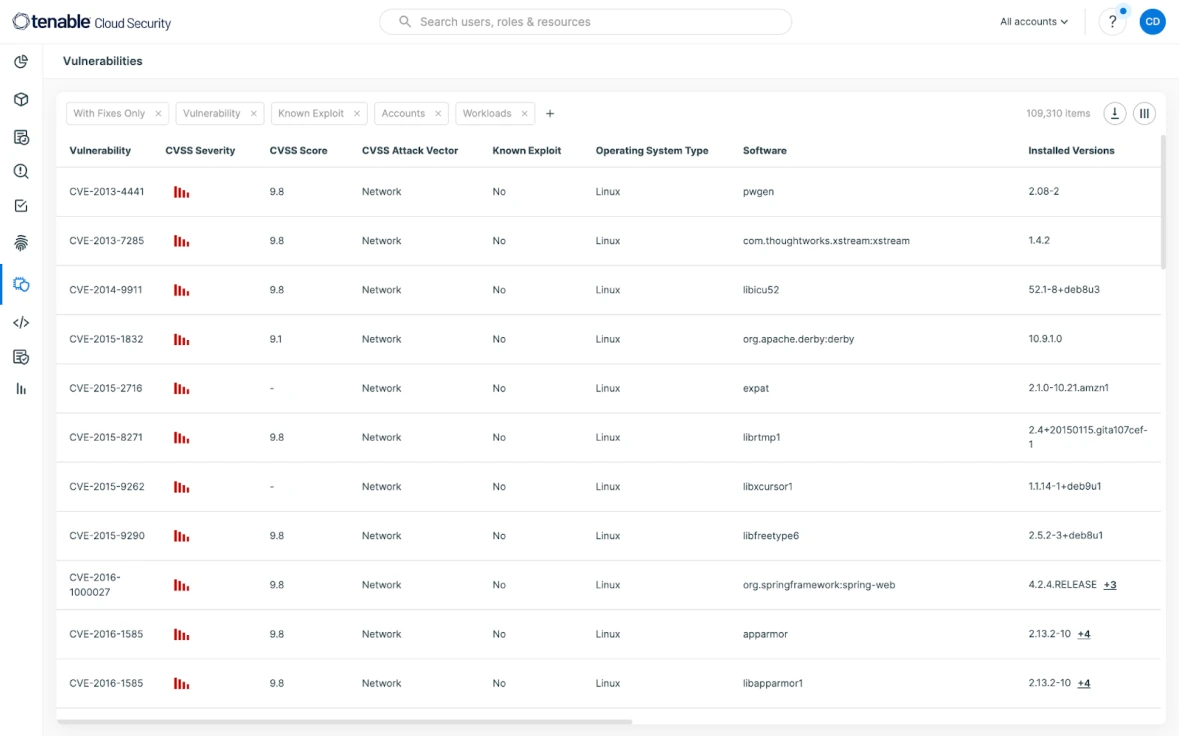
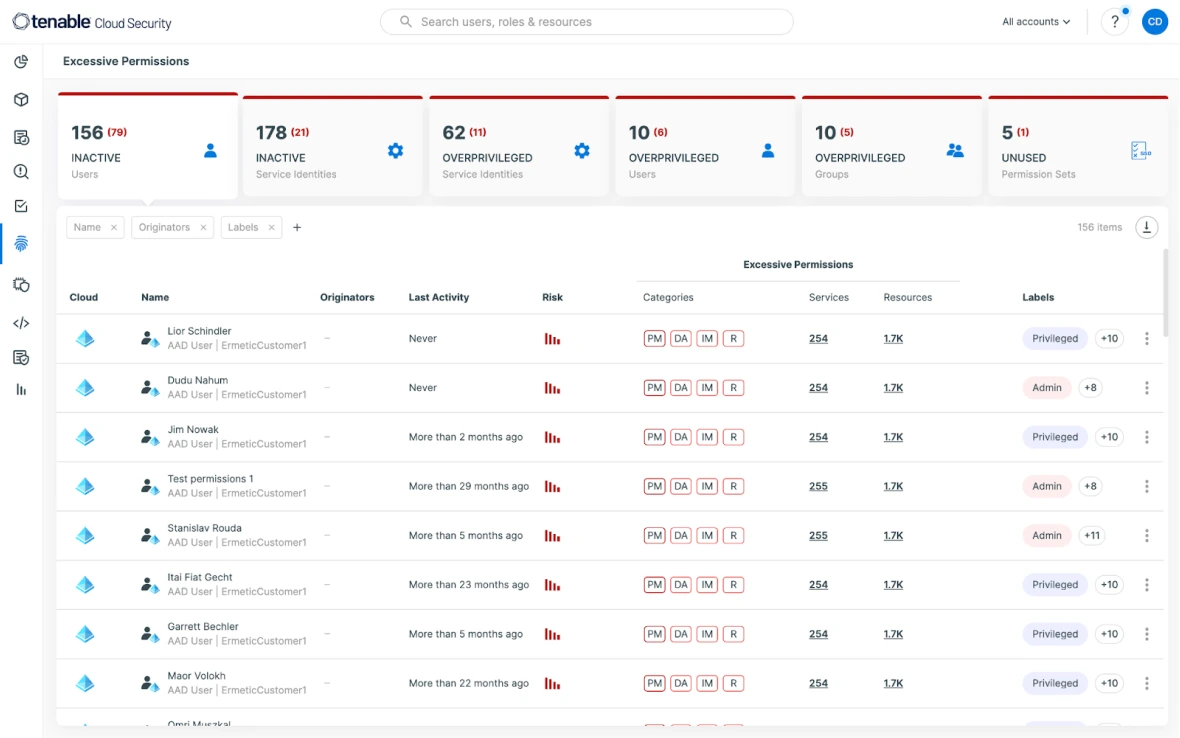
Build zero trust in your cloud security infrastructure. Minimice los permisos en exceso para los servicios y los humanos, sin descomponer nada. La ruta hacia los privilegios mínimos comienza con una imagen completa y precisa de todos los derechos. Continuously discover all entities and policies (including IAM, resource, permissions boundaries, and ACLs) in the environment and analyze the relationships to reveal the gap between desired enterprise policy and actual entitlements.
Try for free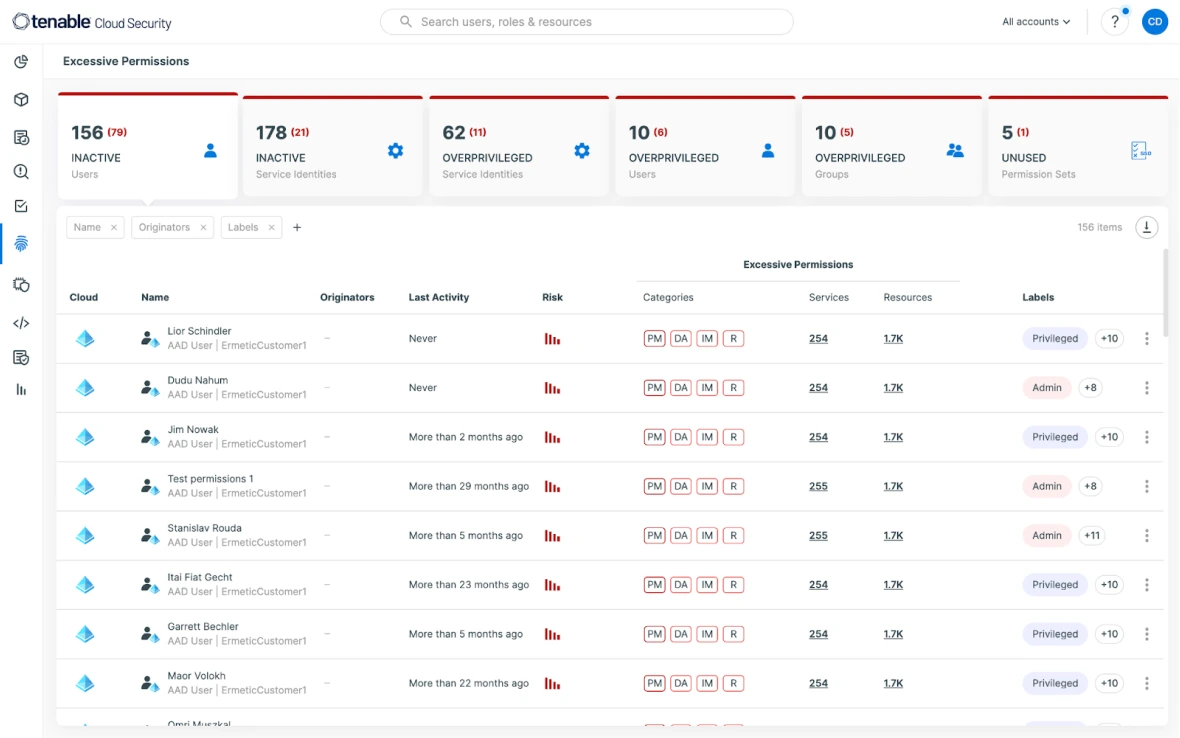




Lea el libro electrónico para obtener la siguiente información:
- How to protect workloads and manage vulnerabilities
- Securing identities and entitlements and enforcing least privilege
- Ways to accelerate cloud detection and response
- How to assess and prioritize risk across cloud environments