Cloud infrastructure entitlement management (CIEM)
Robust identity-first entitlement management for AWS, Azure and GCP
Cloud identities - human and service - and their access to data are the leading cause of cloud breaches. Attackers exploit unauthorized access, toxic combinations, and other risks to gain entry. Cloud complexity makes misconfigured and excessive permissions hard to spot and fix. Tenable Cloud Security brings industry-leading identity-first CIEM to your doorstep.
Request a demo of Tenable Cloud Security
Exceptional unified cloud security awaits you!
We'll show you exactly how Tenable Cloud Security helps you deliver multi-cloud asset
discovery, prioritized risk assessments, and
automated compliance/audit reports.
More than 44,000+ organizations around the world rely on Tenable to better understand and reduce cybersecurity risk.
Cloud security that
fits your unique journey
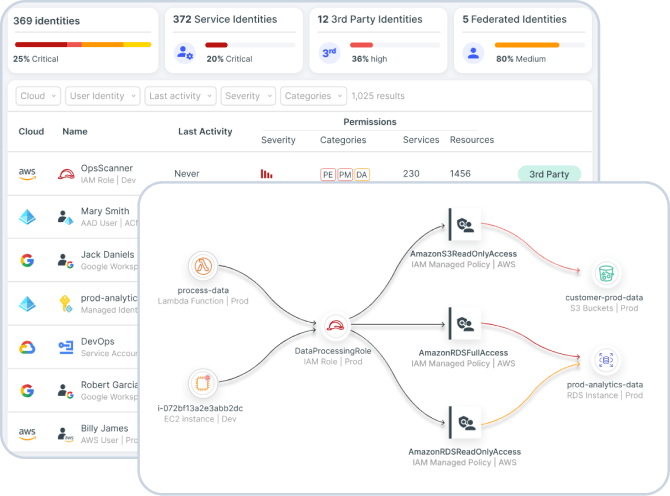
Manage a full inventory of identities, entitlements, resources, and configurations in your cloud infrastructure, visualizing permissions and relationships. Detect and prioritize entitlement risk with pinpoint accuracy and remediate via least privilege automated workflows.
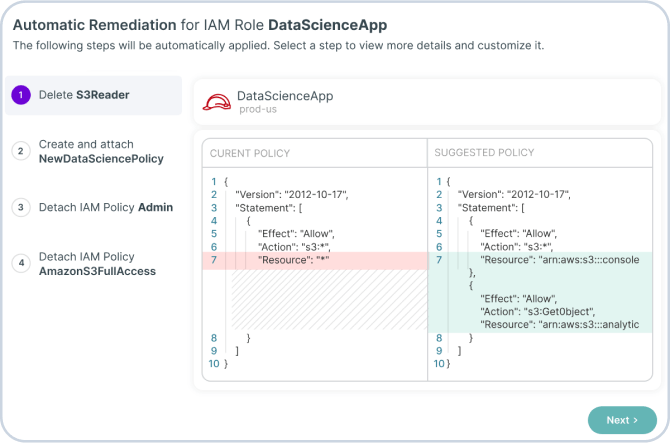
Get in touchRemove risky entitlements and misconfigurations quickly using automated and guiding remediation tools. Use wizards for direct remediation, send generated optimized policies in existing workflows (e.g. Jira, ServiceNow), and deliver right-sized code snippets to developers.
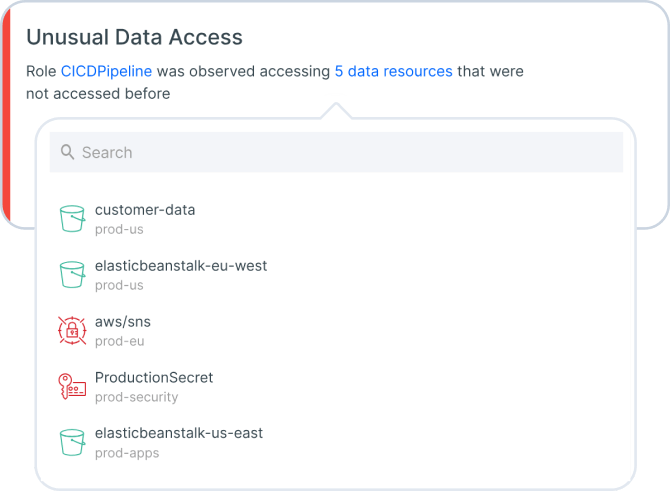
Get in touchPerform risk analysis against behavioral baselines, spotting suspicious activity. Identify identity-based threats related to data access, network access, permissions, and more. Query enriched logs and accelerated incident response through integrations with SIEM and ticketing.
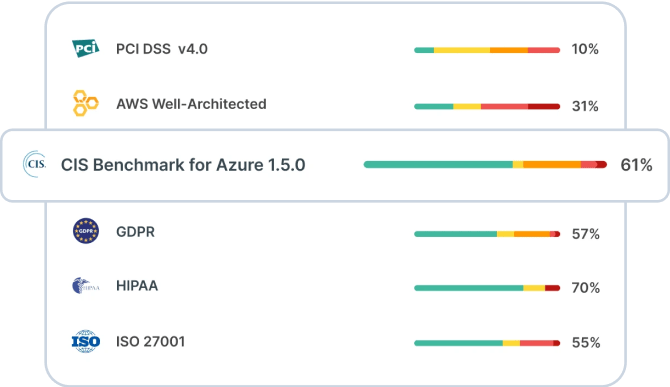
Get in touchContinuously audit and report in detail to stakeholders on how your privileged cloud identities are being used and the underlying authorization process. Comply with industry regulations that require cloud security capabilities to govern access policy and enforce least privilege.
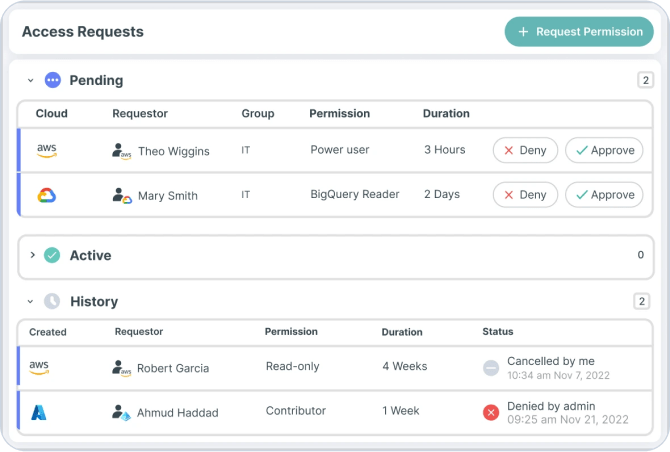
Get in touchMinimize attacker risk by empowering engineering teams to easily request and gain authorized approval to temporary elevated access based on business justification. Use Tenable JIT to enforce least privilege and avoid standing privileges. Maintain an audit trail of all JIT activity.
Get in touch