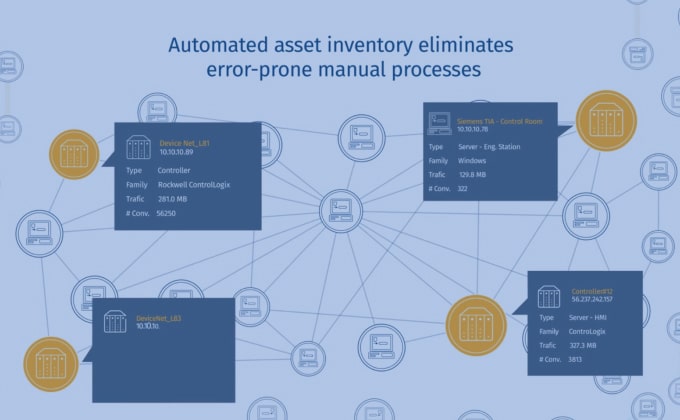
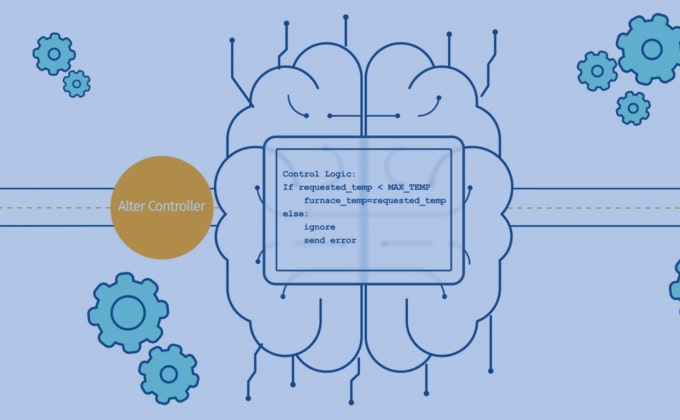
Gain Control of Any Changes Made to the Manufacturing Process with Configuration Control
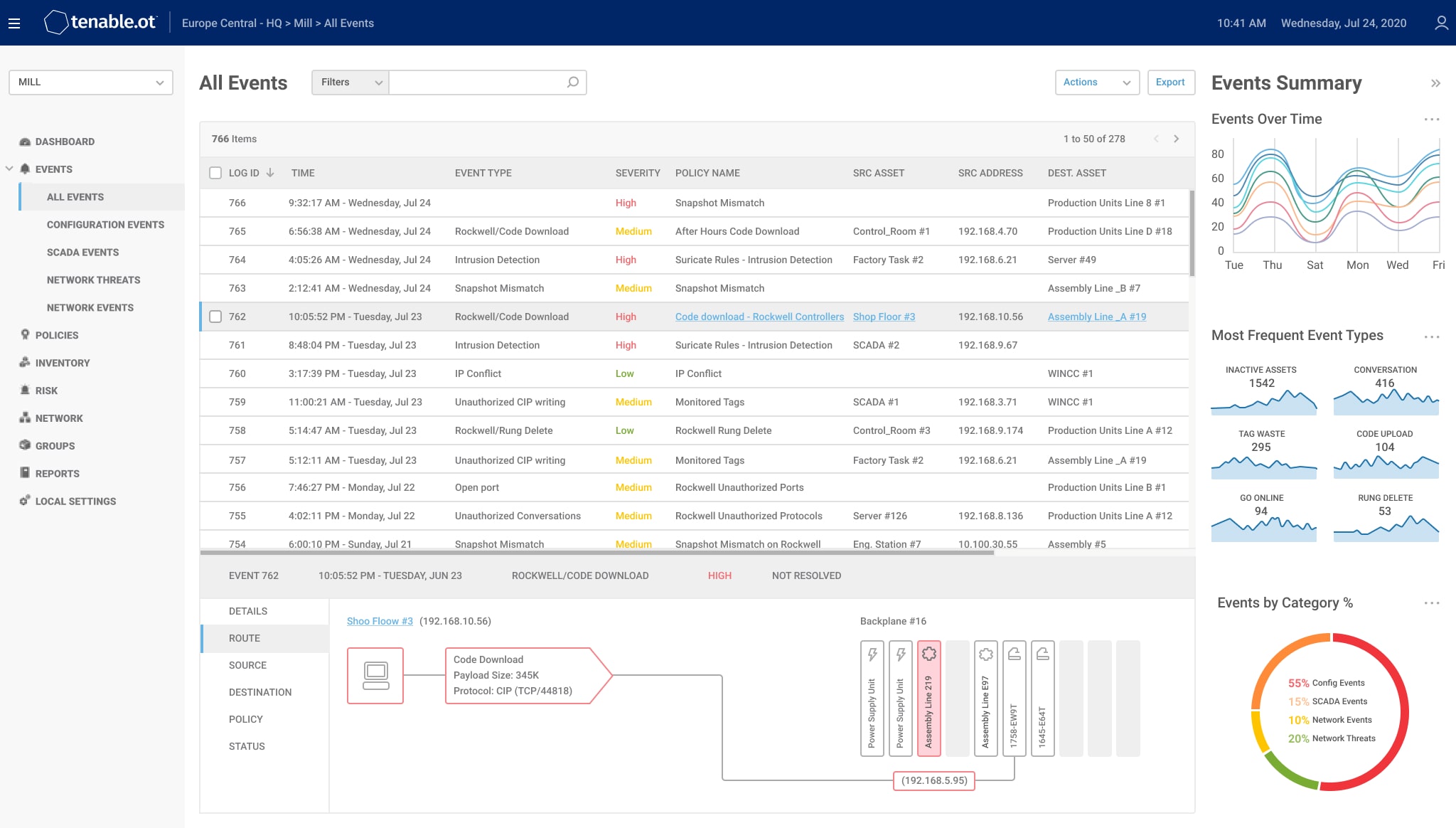
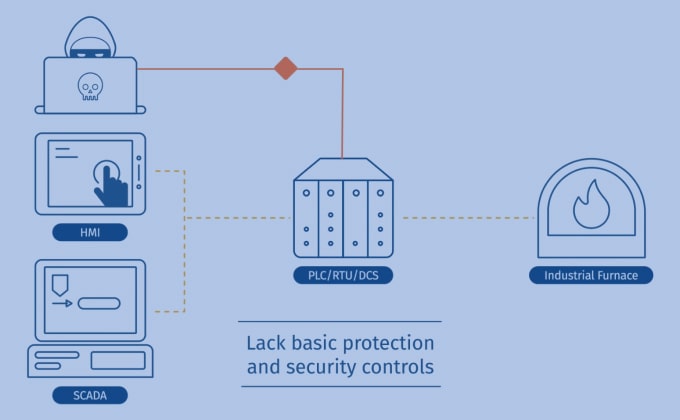
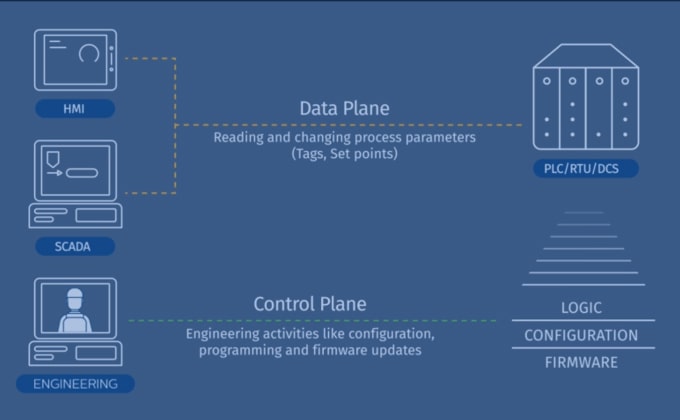
Unauthorized changes to the pharma manufacturing process - due to cyber attack or human error - can severely impact product quality and public health, as well as causing lengthy downtime, revenue losses and reputation damage.