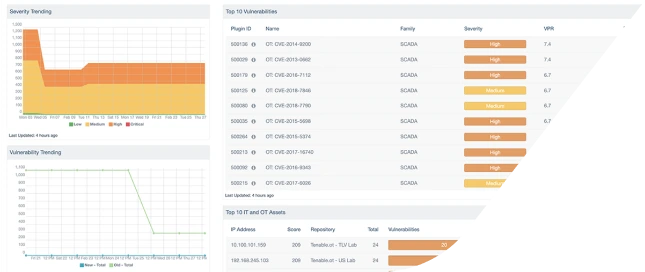
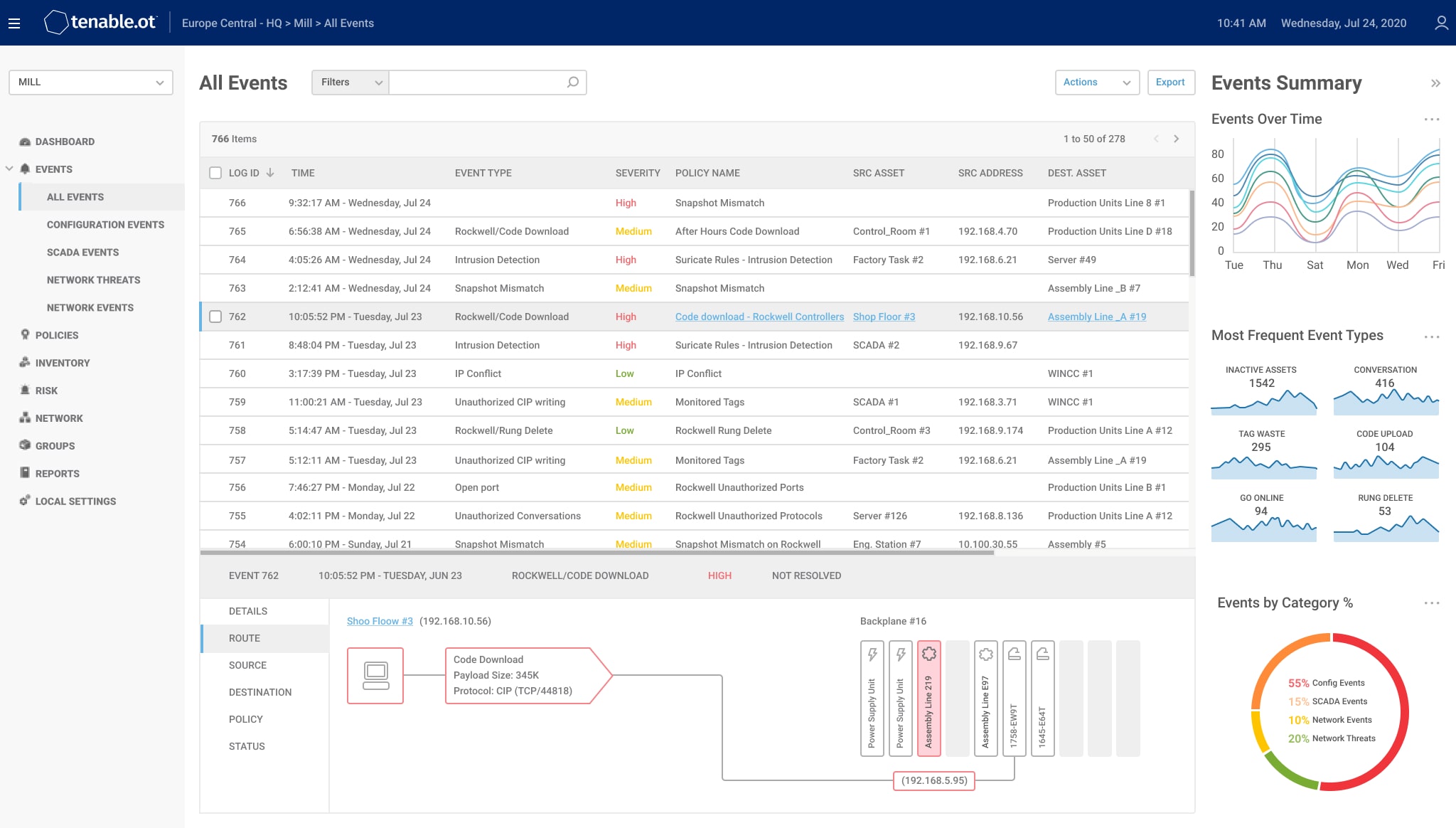
Define rules and enforce security policy on your building management system.
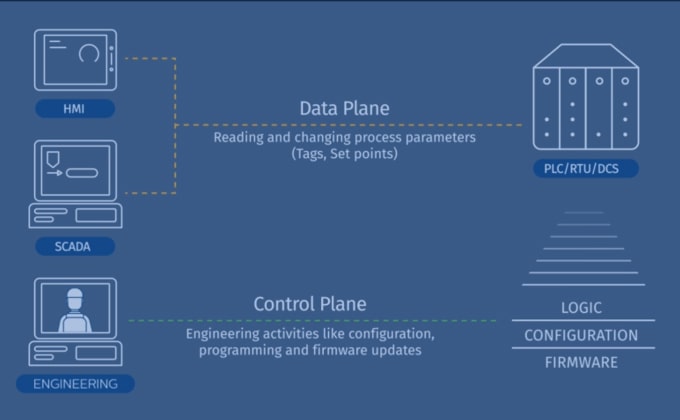
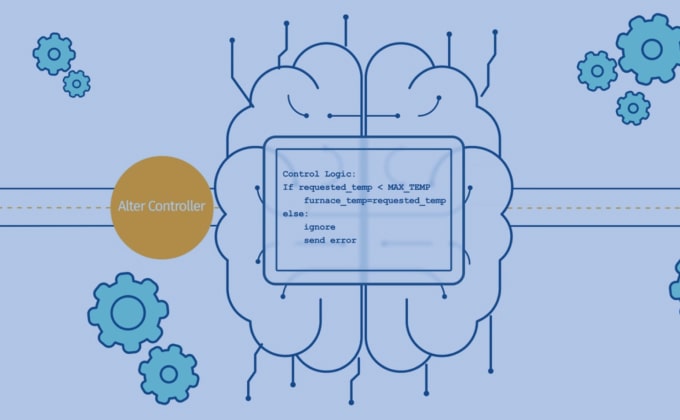
Tenable.ot provides a flexible, intuitive interface that enables you to define security rules for
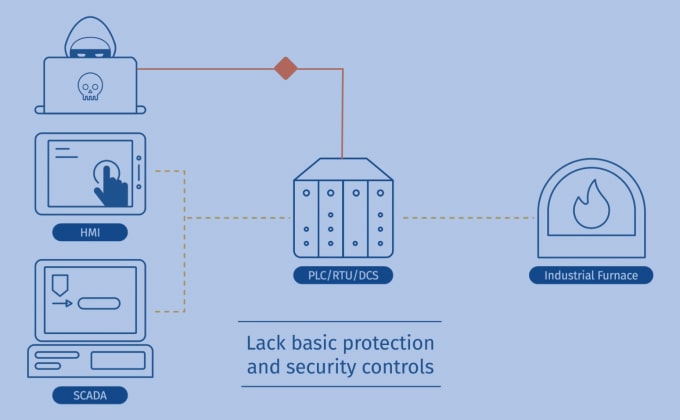
your specific BMS environment. In accordance with your security policy, Tenable.ot rules trigger
alerts about risky activities, suspicious network events or logic changes, or deviations from
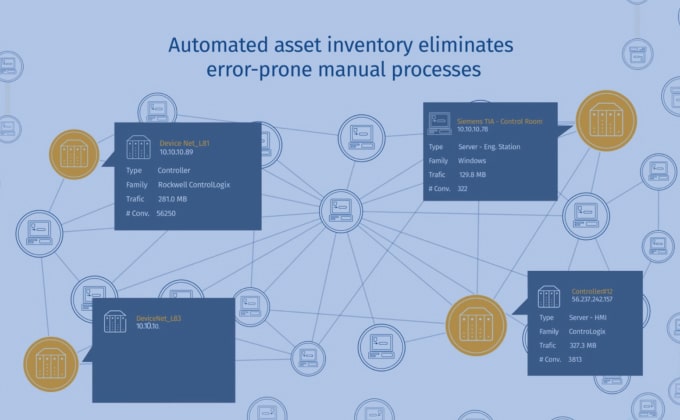
compliance requirements. Tenable.ot automates the enforcement of security policies for multi-vendor
environments, eliminating the need for inefficient and error-prone manual procedures.