by David Schwalenberg
May 17, 2017
Network vulnerabilities can lead to critical failures of devices, dangerous network attacks and compromise of sensitive data. The financial industry is highly targeted by cyber attacks, emphasizing the urgent need for robust cyber security and increased network resilience.
In 2016, due to the increasing use of information technology by banks and their customers, and the increase in cyber attacks against the financial sector, the Reserve Bank of India (RBI) provided guidelines in the area of cyber security to banks. The guidelines document, Cyber Security Framework in Banks, includes an Annex detailing minimum baseline requirements for network security and resilience. These requirements cover such areas as inventory management, secure configuration, patch management, access control and advanced real-time threat defense.
Tenable's Tenable.sc Continuous View® (Tenable.sc CV™) offers several specialized dashboards that can help banks comply with the requirements specified in the RBI document. This dashboard assists in the areas of vulnerability and patch management, and aligns with paragraph 6 ("Testing for vulnerabilities at reasonable intervals...") of the RBI document, as well as baseline controls 7 (Patch/Vulnerability and Change Management) and 18 (Vulnerability Assessment) in Annex 1.
New vulnerabilities are constantly being discovered and a goal of eliminating all network vulnerabilities is unrealistic. However, by prioritizing vulnerability remediations and tracking patch management progress, the risk can be reduced to a manageable level in a timely manner.
This dashboard assists an organization in prioritizing vulnerability remediations. Exploitable vulnerabilities – particularly externally accessible ones – are especially important to eliminate, as the means to exploit these vulnerabilities are already known to exist. Detecting vulnerabilities per asset group enables the organization to focus remediation efforts in areas where those efforts are most needed. Top remediation opportunities indicate which patches and updates can be applied to most reduce risk on the network.
The dashboard also assists in tracking remediation progress. A trend and counts of mitigated and unmitigated vulnerabilities are presented by vulnerability severity. Continuous vulnerability scanning can be monitored by the percentages of machines with recent active and passive detections of vulnerabilities. Vulnerabilities reported by specific patch management solutions enable monitoring the effectiveness of those solutions.
The components on this dashboard provide clear information about vulnerabilities detected in the environment and help to identify where vulnerability remediation efforts can best pay off for the organization. Having accurate information to confidently address vulnerabilities and track remediation progress will assist an organization in securing the network and complying with the RBI requirements.
This dashboard is available in the SecurityTenable.scCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.5
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
Tenable's Tenable.sc CV is the market-defining continuous network monitoring solution, and assists in securing an organization’s internal network. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new regulatory compliance data. Active scanning periodically examines systems to detect vulnerabilities within operating systems, software applications and hardware. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities in operating systems, protocols, network services, wireless devices, web applications and critical infrastructure. Host data and data from other security products, such as patch management solutions, is analyzed to monitor mitigation progress. Tenable.sc CV provides the organization with the most comprehensive view of the network and the intelligence needed to effectively address vulnerabilities.
The following components are included in this dashboard:
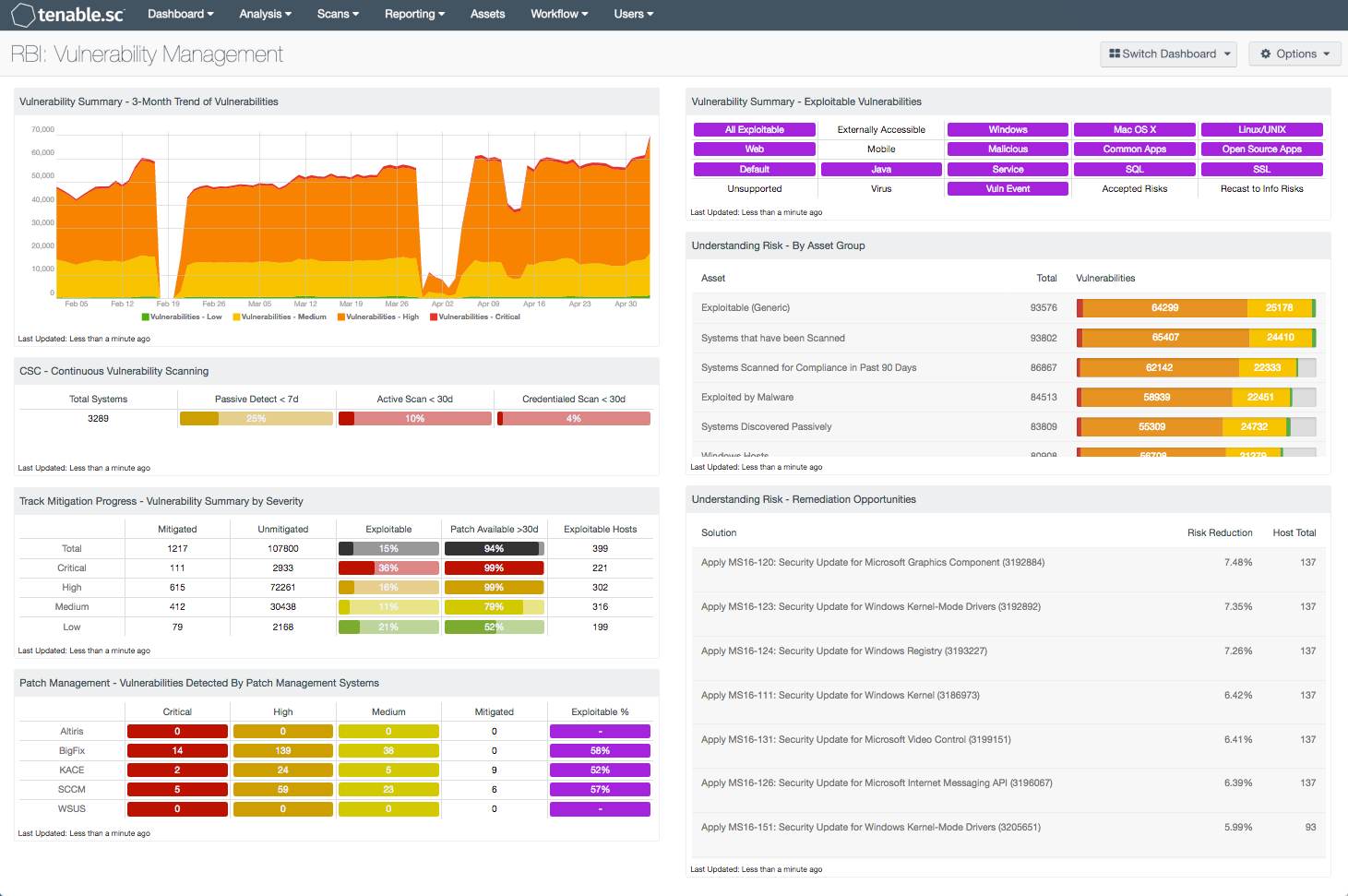
- Vulnerability Summary - 3-Month Trend of Vulnerabilities: This component is a 3-month summary chart tracking unmitigated vulnerabilities of low, medium, high and critical severity.
- CSC - Continuous Vulnerability Scanning: This matrix assists in monitoring vulnerability detection and scanning by displaying the percentages of total systems that have had recent passive vulnerability detections, active vulnerability scans and credentialed scans.
- Track Mitigation Progress - Vulnerability Summary by Severity: Tenable.sc records when vulnerabilities are discovered, when patches are issued and when vulnerabilities are mitigated. This component assists in tracking vulnerability mitigations.
- Patch Management - Vulnerabilities Detected by Patch Management Systems: This matrix presents an overview of detected vulnerabilities reported by several patch management systems.
- Vulnerability Summary - Exploitable Vulnerabilities: This matrix displays warning indicators for known exploitable vulnerabilities actively and passively detected on the network.
- Understanding Risk - By Asset Group: This table presents a summary by asset grouping of vulnerabilities found to exist in the environment.
- Understanding Risk - Remediation Opportunities: This table displays the top remediations for the network.