by Megan Daudelin
May 4, 2017
Intel has released information about a major vulnerability that allows unprivileged attackers to gain control over certain manageability features through privilege escalation. The vulnerability is present in Intel® Active Management Technology (AMT), Intel® Standard Manageability (ISM) and Intel® Small Business Technology (SBT) firmware versions 6.x, 7.x, 8.x 9.x, 10.x, 11.0, 11.5 and 11.6. By leveraging scan data from Tenable Nessus® and Tenable Passive Vulnerability Scanner® (PVS™), Tenable SecurityCenter® can provide insight into the systems in the organization that are potentially or certainly impacted by this vulnerability.
There are two specific ways that the vulnerability in the noted Intel chipsets can be exploited. First, an unprivileged network attacker could gain system privileges to provisioned Intel manageability products including AMT and ISM. Second, an unprivileged local attacker could provision manageability features gaining unprivileged network or local system privileges on Intel manageability products including AMT, ISM and SBT. Security teams should note that this vulnerability will not be remediated as part of normal patch releases and the affected firmware will need to be patched or updated manually. Intel recommends first checking with the system OEM for firmware updates, and has provided instructions on detecting vulnerable hosts and mitigating risk to hosts without firmware patches available.
The INTEL-SA-00075 Detection dashboard is able to leverage data gathered by Nessus and PVS in order to alert security teams to potentially vulnerable hosts on their network. Several plugins provide detailed information that can indicate the use of vulnerable firmware. Such plugins operate by enumerating services and installed software during credentialed scans. Additionally, the Intel Active Management Server Detection passive plugin (ID 6955) identifies hosts that are Intel Active Management servers, meaning they can be remotely administered even when off. Newly released active plugins (IDs 97997 and 97998) are also able to identify hosts with vulnerable Intel processors. The passive and active data should be used to prioritize vulnerable hosts for firmware patching. For additional information about the INTEL-SA-00075 vulnerability, review Intel’s security advisory and Tenable’s blog post.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.4.5
- Nessus 6.10.5
- PVS 5.2.0
Tenable SecurityCenter is the market-defining continuous network monitoring solution, and can assist in securing an organization’s internal network and effectively remediating new vulnerabilities. SecurityCenter is continuously updated with information about advanced threats, zero-day vulnerabilities and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications and critical infrastructure. SecurityCenter provides an organization with the most comprehensive view of the network and the intelligence needed to support effective vulnerability remediation efforts.
The following components are included in this dashboard:
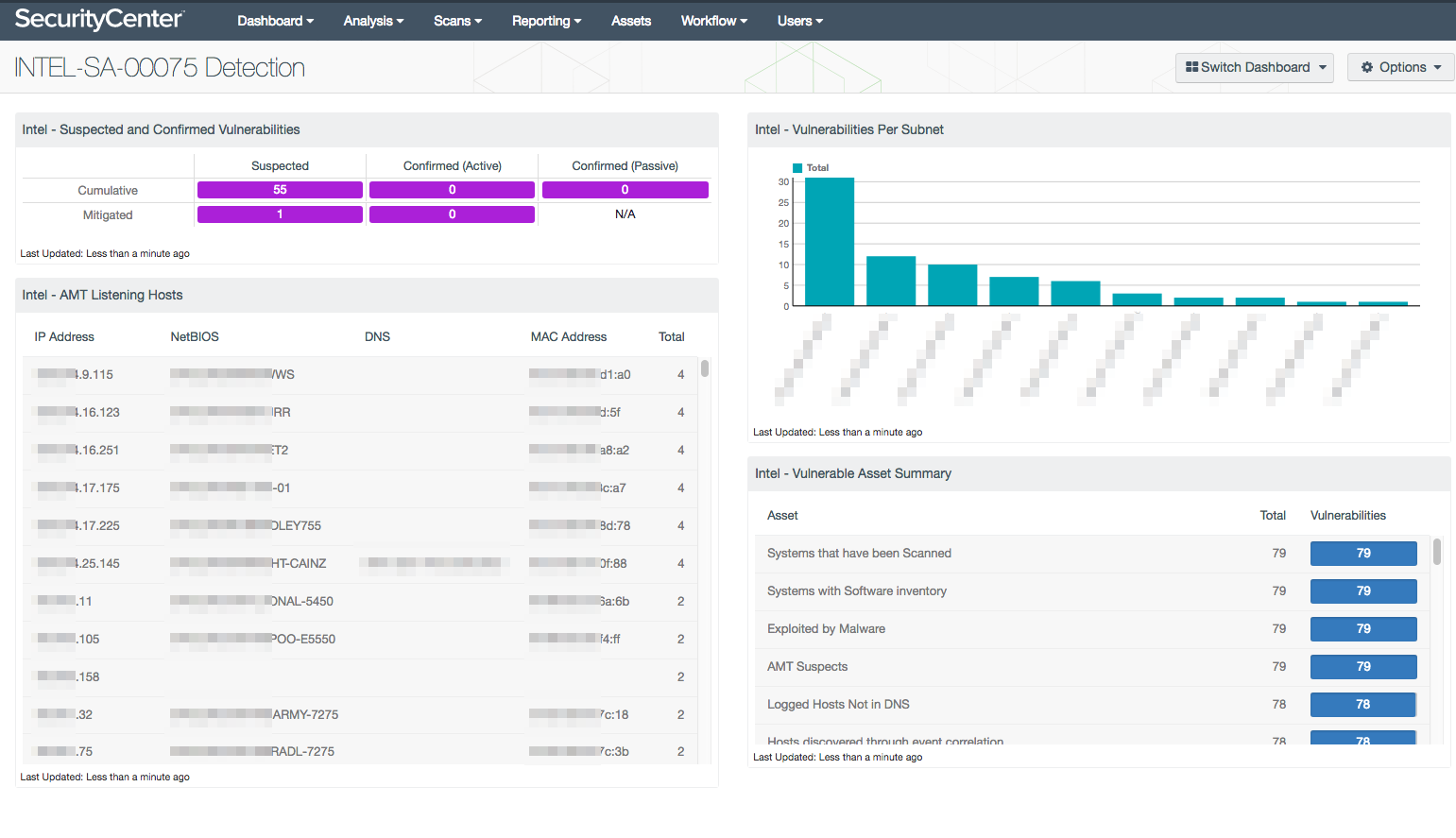
- Intel – Suspected and Confirmed Vulnerabilities: This matrix displays counts of detected vulnerabilities that are suspected or confirmed to be related to the INTEL-SA-00075 vulnerability.
- Intel – AMT Listening Hosts: This table identifies hosts that are listening on ports 16992-16995, 623 and 664, the ports associated with Intel Active Management Technology.
- Intel – Vulnerabilities Per Subnet: This bar chart lists the subnets that contain hosts with vulnerabilities related to INTEL-SA-00075.
- Intel – Vulnerable Asset Summary: This table lists the assets with plugin detections related to the INTEL-SA-00075 vulnerability by total count.