Intel AMT Back in the News

The release of new research from F-Secure spells more trouble for Intel’s Active Management Technology (AMT). AMT is used for remote access monitoring and maintenance in corporate environments. Previously, in 2017, researchers discovered a critical vulnerability with AMT that made headlines. The previous vulnerability was a wide-reaching privilege escalation vulnerability (INTEL-SA-00075, CVE-2017-5689). Now, AMT is in the news again this week, as another serious security issue has been disclosed. The issue was discovered by a security researcher with the Finnish security company F-Secure. It could allow an attacker who has physical access to an affected device to enable the technology’s remote access features, letting them take complete control of a machine while on the same network segment.
Details
The F-Secure advisory explains that an attacker who has physical access to the device can simply reboot the machine and press CTRL+P during bootup to access the Intel Management Engine BIOS Extension (MEBx) login. If Intel AMT hasn’t already been provisioned by the device owner or corporate IT, the MEBx login is only protected by a default password of admin. By accessing the MEBx configuration, an attacker could enable remote access and set AMT’s user opt-in to “None,” allowing the attacker to gain remote access to the device without the user’s consent. This gives the attacker the ability to take full control of the machine if they’re on the same wired or wireless network.
While the likelihood of an attack is decreased due to the requirement of physical access to the device, the exploitation of this issue is both extremely simple and takes very little time to execute for a reasonably skilled attacker. Security professionals often warn users not to leave a laptop in a hotel room or other unsecured location where the device is unattended. If the computer is left unattended, the attacker has an opportunity to reboot the system, alter the MEBx configuration and be gone – all before the user returns. A simple flaw such as this becomes a gold mine for an attacker determined to target an individual or organization.
Detection methods
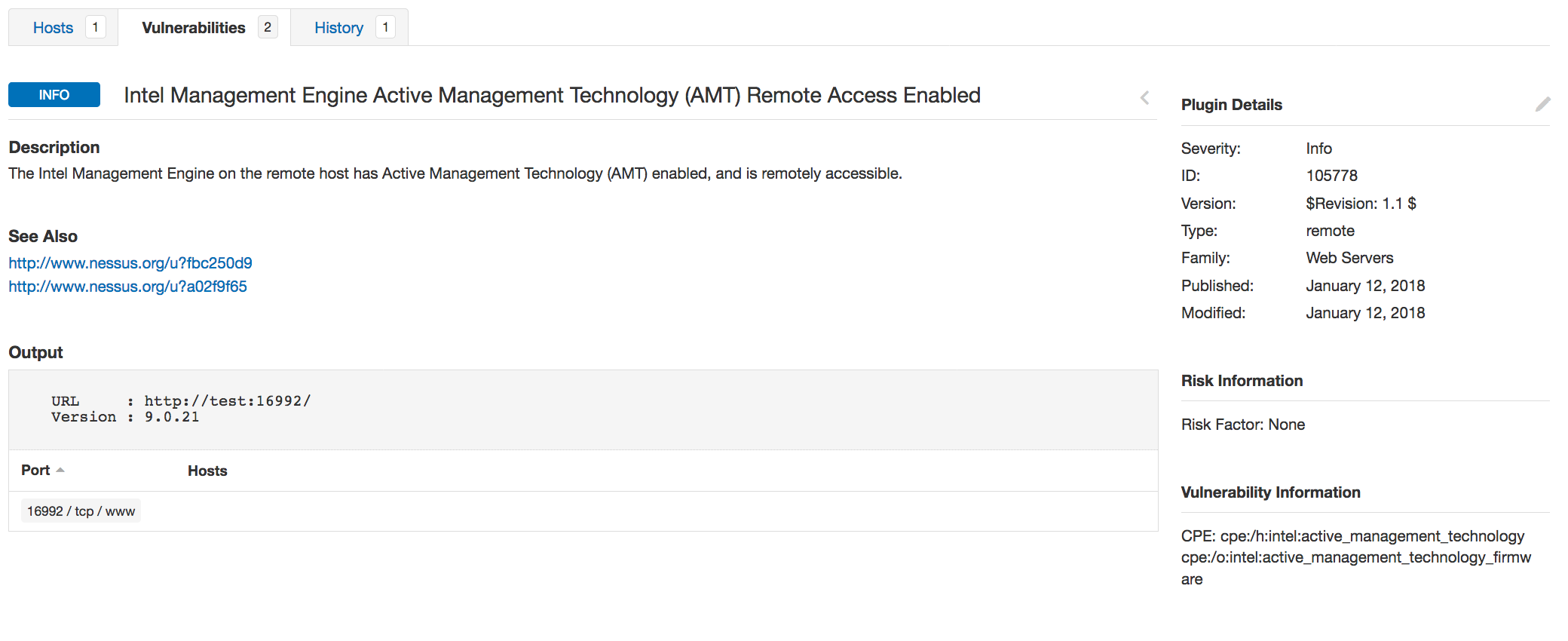
New plugins have been released for Tenable.io Vulnerability Management, SecurityCenter and Nessus to determine whether a device has Intel AMT remote access enabled and running. Plugin #105778, Intel Management Engine Active Management Technology [AMT] Remote Access Enabled, detects whether the Intel AMT remote access feature is enabled based on the banner of the service listening on port 16992. Using a previously released plugin, #102992, Intel Active Management Technology (AMT) detection, you can identify systems potentially at risk for this new vulnerability without scanning again.
Scan policy modifications
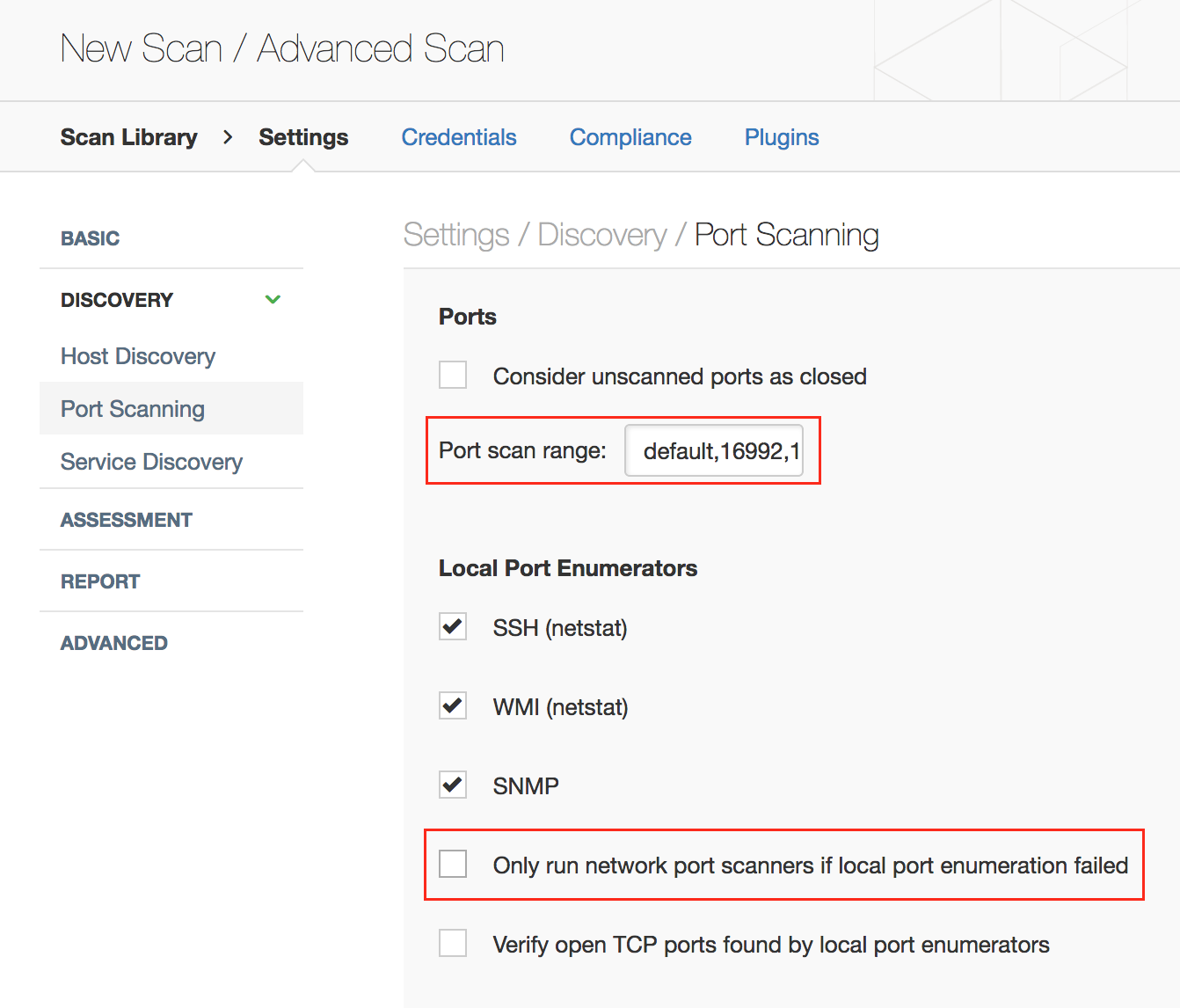
The default port scanning preferences need to be modified to enable detection of this vulnerability. The port scanning preferences need to be set to probe ports 16992, 16993 and 623 as well as the default ports. Also, you should scan the system using the SYN and TCP network scanners in addition to the local scanner option, as the local enumerator is unable to enumerate the Intel AMT ports.
To check whether your system supports Intel AMT, you can use the plugins mentioned above. Alternatively, you may check your BIOS manually for Intel AMT and MEBx technologies by pressing CTRL-P during the boot process. Intel has also provided a reference document to help determine if you have an Intel AMT, Intel SBA or Intel ISM capable system.
Wrapping up – what you can do right now
Here are a few suggestions on what you can do right now to protect your organization from this newly discovered vulnerability:
- If your organization has devices that support Intel AMT technology and the Intel Management Engine BIOS Extension, log into the MEBx menu and set a strong password to replace the default password of admin. And if you don’t plan to use Intel AMT, consider disabling it.
- Given the physical proximity required for this particular attack to be executed, remind users to always be mindful of operational security: Don’t leave laptops unattended in unsecured locations.
- Get plugin #105778, Intel Management Engine Active Management Technology [AMT] Remote Access Enabled, which detects whether the Intel AMT remote access feature is enabled based on the banner of the service listening on port 16992.
- Learn more about Tenable.io, which we continuously update, so you can detect the latest vulnerabilities quickly.
Artículos relacionados
- Tenable Vulnerability Management (DO NOT USE)







